Home » Posts tagged 'security' (Page 3)
Tag Archives: security
The Ultimate Linux Sandbox in the Cloud for Less Than a $35 Raspberry Pi 2

Every few years we like to drop back and take a fresh look at the best way to get started with Linux. For those coming from the Windows World, it can be a painful process. Learning with a Cloud-based server can be especially dangerous because of the security risks. And then there’s the cost factor. Not everyone has several hundred dollars to buy hardware and, frankly, learning about Linux on a $35 Raspberry Pi can drive most newbies to drink. So today we’ll show you another way. It’s not necessarily a better way. But it’s different, and it’s loads of fun for not much money. Today’s project only takes 30 minutes.
There’s lots to hate at Cloud At Cost, a Canadian provider that offers virtual machines in the cloud for a one-time fee with no recurring charges. For $35 or less, you get a virtual machine with 512MB of RAM, 10GB of storage, and a gigabit Internet connection FOR LIFE. We haven’t seen a week go by when Cloud at Cost didn’t offer some sort of discount. Today it’s 70% off with coupon code TAKE70 which brings the total cost down to $10.50. That’s less than a burger at Five Guys. That’s the good news. But, if security, 99.999% reliability, performance, and excellent customer support are your must-haves, then look elsewhere. So why would anyone in their right mind sign up for a cloud solution that didn’t offer those four things? Did we mention it’s $10.50 for a lifetime cloud server?
If you take our recommendation and plunk down your Alexander Hamilton, you’ll need to go into this with the right attitude. It’s not going to be flawless perfection computing. It’s a sandbox on which to experiment with Linux and Cloud Computing. Will your virtual machine disintegrate at some juncture? Probably. Our experience is that the first couple days are critical. If you start seeing sluggish performance which degenerates to zero, don’t waste your time. Take good notes as you go along, delete the virtual machine, and rebuild a new one. It won’t cost you a dime, and it’ll save you hours of frustration. We suspect that bad folks get onto some of the servers and delight in bringing the machines to their knees. So the quicker you cut your losses, the better off you will be. Is CloudAtCost a good solution for production use? Absolutely not so don’t try to fit a square peg in the round hole. It’s not gonna work, and you WILL be disappointed. You’ve been warned. Let’s get started. ENJOY THE RIDE!
Our objective today is to show you how to build a rock-solid, secure Linux server in the Cloud with all the bells and whistles that make Linux the server platform of choice for almost every organization in the world. We’ll finish up by showing you how to embellish the platform with WordPress to do something that’s special for you whether it’s your own blog like Nerd Vittles, or a school newspaper, or an on-line shopping site to sell comic books. The basic foundation for most Linux platforms is called a LAMP server which stands for Linux, Apache, MySQL, and PHP. Linux is an open source operating system that includes contributions from thousands of developers around the world. Apache is the web server platform on which most commercial businesses stake their reputation. MySQL is the open source database management system now owned by Oracle. If it’s good enough for Facebook, it’s good enough for you. And PHP is THE web-based programming language that will let you build almost any application using Linux, Apache, and MySQL.
So what’s the big deal? There are thousands of online tutorials that will show you how to build a LAMP server. For long time readers of Nerd Vittles, you already know that the component we continually stress is security. Without that, the rest really doesn’t matter. You’ll be building a platform for someone else to hijack and use for nefarious purposes. When we’re finished today, you’ll have a cloud-based server that is totally invisible to the rest of the world with the exception of its web interface. And we’ll show you a simple way to reduce the exposure of your web interface to some of its most likely attackers. Will it be 100% secure? Nope. If you have a web server on the public Internet, it’s never going to be 100% secure because there’s always the chance of a software bug that nobody has yet discovered and corrected. THAT’S WHAT BACKUPS ARE FOR!
Creating Your Virtual Machine Platform in the Cloud
To get started, you’ve got to plunk down your $10.50 at Cloud at Cost using coupon code TAKE70. Once you’ve paid the piper, they will send you credentials to log into the Cloud at Cost Management Portal. Change your password IMMEDIATELY after logging in. Just go to SETTINGS and follow your nose.
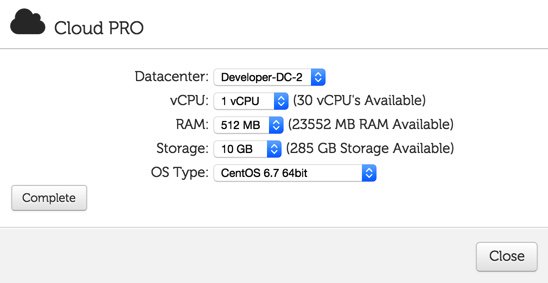
To create your virtual machine, click on the CLOUDPRO button and click Add New Server. If you’ve only purchased the $10.50 CloudPRO 1 platform, then you’ll need all of the available resources shown in the pick list. Leave CentOS 6.7 64bit selected as the OS Type and click Complete. Depending upon the type of special pricing that Cloud at Cost is offering when you sign up, the time to build your virtual machine can take anywhere from a minute to the better part of a day. We’ve learned to build new virtual machines at night, and they’re usually available for use by the next morning. Luckily, this slow performance does not impact existing virtual machines that already are running in their hosting facility.
Initial Configuration of Your CentOS 6.7 Virtual Machine
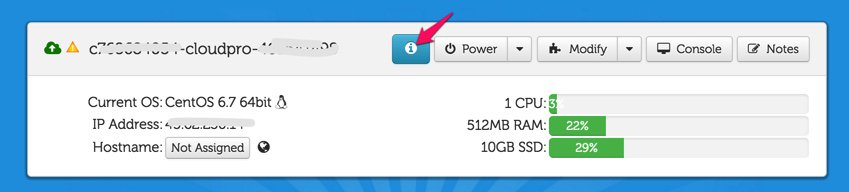
With a little luck, your virtual machine soon will appear in your Cloud at Cost Management Portal and look something like what’s shown above. The red arrow points to the i button you’ll need to click to decipher the password for your new virtual machine. You’ll need both the IP address and the password for your new virtual machine in order to log into the server which is now up and running with a barebones CentOS 6.7 operating system. Note the yellow caution flag. That’s telling you that Cloud at Cost will automatically shut down your server in a week to save (them) computing resources. You can change the setting to keep your server running 24/7. Click Modify, Change Run Mode, and select Normal – Leave Powered On. Click Continue and OK to save your new settings.

Finally, you’ll want to change the Host Name for your server to something more descriptive than c7…cloudpro.92… Click the Modify button again and click Rename Server to make the change. Your management portal then will show the new server name as shown above.
Logging into Your CentOS 6.7 Virtual Machine
In order to configure and manage your new CentOS 6.7 virtual machine, you’ll need to log into the new server using either SSH or, for Windows users, Putty. After installing Putty, run it and log in to the IP address of your VM with username root and the password you deciphered above. On a Mac, open a Terminal session and issue a command like this using the actual IP address of your new virtual machine:
ssh root@12.34.56.78
Before you do anything else, reset your root password to something very secure: passwd
Installing the LAMP Server Basics with CentOS 6.7
Now we’re ready to build your LAMP server platform. We’ve chopped this up into lots of little steps so we can explain what’s happening as we go along. There’s nothing hard about this, but we want to document the process so you can repeat it at any time. As we go along, just cut-and-paste each clump of code into your SSH or Putty session and review the results to make sure nothing comes unglued. If something does, the beauty of virtual machines is you can delete them instantly within your management portal and just start over whenever you like. So here we go…
We’ll begin by permanently turning off SELINUX which causes more problems than it solves. The first command turns it off instantly. The second line assures that it’ll stay off whenever you reboot your virtual machine.
setenforce 0 sed -i s/SELINUX=enforcing/SELINUX=disabled/g /etc/selinux/config
Now let’s bring CentOS 6.7 up to current specs and add a few important applications:
yum -y update yum -y install nano wget expect net-tools dialog git xz yum -y install kernel-headers yum -y install kernel-devel reboot
After reboot, log back in as root. Now we’ll set up your Apache web server and configure it to start whenever you reboot your server:
yum -y install httpd service httpd start chkconfig httpd on
Now let’s set up your MySQL server, bring it on line, and make sure it restarts after server reboots. Unless you plan to add Asterisk® and FreePBX® to your server down the road, you’ll want to uncomment the two commands that begin with # by removing the # symbol and replacing new-password with a very secure password for your root user account in MySQL. Be sure to run the last command to secure your server. After logging in, the correct answers are n,Y,Y,Y,Y.
yum -y install mysql mysql-server service mysqld start chkconfig mysqld on #/usr/bin/mysqladmin -u root password 'new-password' #/usr/bin/mysqladmin -u root -p -h localhost.localdomain password 'new-password' mysql_secure_installation
Next, we’ll set up PHP and configure it to work with MySQL:
yum -y install php yum -y install php-mysql service httpd restart
Finally let’s get SendMail installed and configured. Insert your actual email address in the last line and send yourself a test message to be sure it’s working. Be sure to check your spam folder since the message will show a sender address of localhost which many email systems including Gmail automatically identify as spam.
yum -y install sendmail rpm -e postfix service sendmail restart yum -y install mailx echo "test" | mail -s testmessage youracctname@yourmailserver.com
Installing Supplemental Repositories for CentOS 6.7
One of the beauties of Linux is not being totally dependent upon CentOS for all of your packaged applications. Let’s add a few other repositories that can be used when you need to add a special package that is not in the CentOS repository. Let’s start with EPEL. We’ll disable it by default and only use it when we need it.
yum -y install http://download.fedoraproject.org/pub/epel/6/x86_64/epel-release-6-8.noarch.rpm sed -i 's|enabled=1|enabled=0|' /etc/yum.repos.d/epel.repo
We actually need the EPEL repo to install Fail2Ban for monitoring of attacks on certain Linux services such as SSH:
yum --enablerepo=epel install fail2ban -y cd /etc wget http://incrediblepbx.com/fail2ban-lamp.tar.gz tar zxvf fail2ban-lamp.tar.gz
We also need the EPEL repo to install ipset, a terrific addition to the IPtables Linux firewall that lets you quickly block entire countries from accessing your server:
yum --enablerepo=epel install ipset -y
Next, we’ll add a sample script that documents how the country blocking mechanism works with ipset.1 For a complete list of countries that can be blocked, go here. If you need a decoder badge to match abbreviations against country names, you’ll find it here. To add other countries, simply edit the shell script and clone lines 4-7 using the names of the countries and country zone files that you wish to add. Be sure to insert the new lines before the commands to restart iptables and fail2ban. This script will need to be run each time your server reboots and before IPtables is brought on line. We’ll handle that a little later.
echo "#\\!/bin/bash" > /etc/block-china.sh echo " " >> /etc/block-china.sh echo "cd /etc" >> /etc/block-china.sh echo "ipset -N china hash:net" >> /etc/block-china.sh echo "rm cn.zone" >> /etc/block-china.sh echo "wget -P . http://www.ipdeny.com/ipblocks/data/countries/cn.zone" >> /etc/block-china.sh echo "for i in \$(cat /etc/cn.zone ); do ipset -A china \$i; done" >> /etc/block-china.sh echo "service iptables restart" >> /etc/block-china.sh echo "service fail2ban restart" >> /etc/block-china.sh sed -i 's|\\\\||' /etc/block-china.sh chmod +x /etc/block-china.sh
Another important repository is REMI. It is especially helpful if you decide to upgrade PHP from the default version 5.3 to one of the newer releases: 5.5 or 5.6. In this case, you’ll want to activate the specific repository to support the release you choose in /etc/yum.repos.d/remi-safe.repo.
yum -y install http://rpms.famillecollet.com/enterprise/remi-release-6.rpm sed -i 's|enabled=1|enabled=0|' /etc/yum.repos.d/remi-safe.repo
One final repository to have on hand is RPMForge, now renamed RepoForge. We’ll use it in a bit to install a dynamic DNS update utility which you actually won’t need at CloudAtCost since your server is assigned a static IP address. But it’s handy to have in the event you wish to assign a free FQDN to your server anyway.
yum -y install http://incrediblepbx.com/rpmforge-release-0.5.3-1.el6.rf.x86_64.rpm sed -i 's|enabled = 1|enabled = 0|' /etc/yum.repos.d/rpmforge.repo
Adding a Few Utilities to Round Out Your LAMP Server Deployment
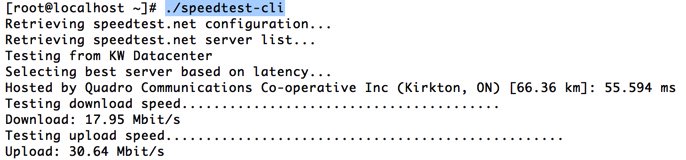
If you’re like us, you’ll want to test the speed of your Internet connection from time to time. Let’s install a free script that you can run at any time by logging into your server as root and issuing the command: /root/speedtest-cli
cd /root wget https://raw.githubusercontent.com/sivel/speedtest-cli/master/speedtest.py chmod +x speedtest.py
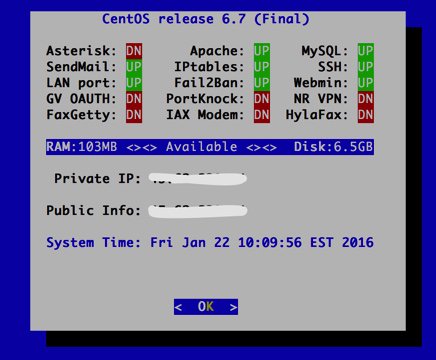
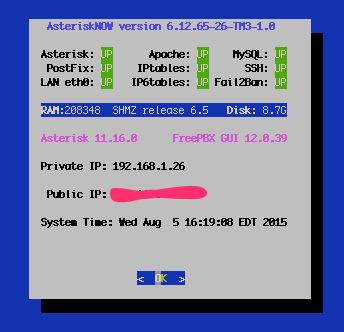
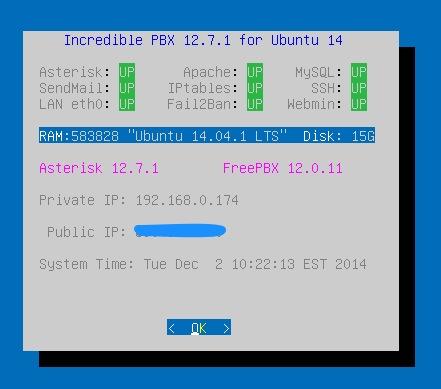
Next, let’s put in place a simple status display which will quickly tell you what’s running and what’s not. We’ve borrowed some GPL code from Incredible PBX to help you out. Run status-lamp at any time for a snapshot of your server.
cd /usr/local/sbin wget http://incrediblepbx.com/status-lamp.tar.gz tar zxvf status-lamp.tar.gz rm -f status-lamp.tar.gz sed -i 's|myip.pbxinaflash.com|myip.incrediblepbx.com|' /usr/local/sbin/status-lamp
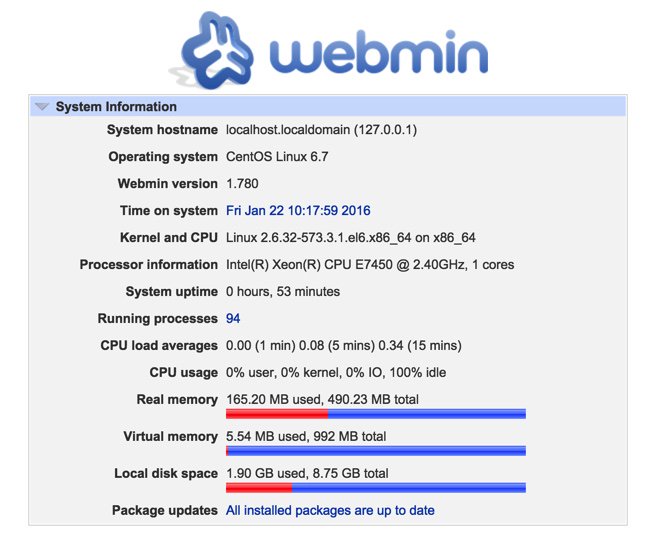
Now we’ll put the Linux Swiss Army Knife in place. It’s called WebMin, and it provides a GUI to configure almost everything in Linux. Pick up a good WebMin book from your public library to get started. Once installed, you access WebMin from your browser at the IP address of your server on the default port of 10000: https://serverIPaddress:10000. It’s probably a good idea to change this port number and the commented out line shows how to do it with the new port being 9001 in the example. The way in which we typically configure the Linux firewall will block all access to WebMin except from an IP address which you have whitelisted, e.g. your home computer’s public IP address.
cd /root yum -y install perl perl-Net-SSLeay openssl perl-IO-Tty yum -y install http://prdownloads.sourceforge.net/webadmin/webmin-1.780-1.noarch.rpm #sed -i 's|10000|9001|g' /etc/webmin/miniserv.conf service webmin restart chkconfig webmin on
Tweaking Your CloudAtCost Setup Improves Performance and Improves Security
Finally, let’s address a couple of CloudAtCost quirks that may cause problems down the road. CloudAtCost has a nasty habit of not cleaning up after itself with fresh installs. The net result is your root password gets reset every time you reboot.
killall plymouthd echo killall plymouthd >> /etc/rc.local rm -f /etc/rc3.d/S97*
With the exception of firewall configuration, which is so important that we’re covering it separately below, you now have completed the LAMP server installation. After completing the firewall steps in the next section, simply reboot your server and you’re ready to go.
The Most Important Step: Configuring the Linux IPtables Firewall
RULE #1: DON’T BUILD SERVERS EXPOSED TO THE INTERNET WITHOUT ROCK-SOLID SECURITY!
As installed by CloudAtCost, your server provides ping and SSH access from a remote computer and nothing else. The good news: it’s pretty safe. The bad news: it can’t do anything useful for anybody because all web access to the server is blocked. We want to fix that, tighten up SSH access to restrict it to your IP address, and deploy country blocking to show you how.
As we implement the firewall changes, you need to be extremely careful in your typing so that you don’t accidentally lock yourself out of your own server. A typo in an IP address is all it takes. The good news is that, if you do lock yourself out, you still can gain access via the CloudAtCost Management Portal by clicking the Console button of your virtual machine. Because the console is on the physical machine and the lo interface is whitelisted, you can log in and disable the firewall temporarily: service iptables stop. Then fix the typo and restart the firewall: service iptables start.
First, let’s download the new IPtables config file into your root folder and take a look at it.
cd /root wget http://incrediblepbx.com/iptables-lamp.tar.gz tar zxvf iptables-lamp.tar.gz
Now edit the /root/iptables-lamp file by issuing the command: nano -w /root/iptables-lamp
You can scroll up and down through the file with Ctl-V and Ctl-Y. Cursor keys work as well. Once you make changes, save your work: Ctl-X, Y, ENTER. You’re now an expert with the nano text editor, an absolutely essential Linux tool.
Here’s what that file actually looks like:
*filter :INPUT DROP [0:0] :FORWARD ACCEPT [0:0] :OUTPUT ACCEPT [0:0] -A INPUT -p tcp -m tcp --tcp-flags ACK ACK -j ACCEPT -A INPUT -m state --state ESTABLISHED,RELATED -j ACCEPT -A INPUT -p icmp -j DROP -A INPUT -i lo -j ACCEPT -A INPUT -p tcp ! --syn -m state --state NEW -j DROP -A INPUT -m state --state INVALID -j DROP -A INPUT -p tcp -m tcp --tcp-flags FIN,SYN,RST,PSH,ACK,URG NONE -j DROP -A INPUT -p tcp -m tcp --tcp-flags SYN,FIN SYN,FIN -j DROP -A INPUT -p tcp -m tcp --tcp-flags SYN,RST SYN,RST -j DROP -A INPUT -p tcp -m tcp --tcp-flags FIN,RST FIN,RST -j DROP -A INPUT -p tcp -m tcp --tcp-flags ACK,FIN FIN -j DROP -A INPUT -p tcp -m tcp --tcp-flags ACK,URG URG -j DROP -A INPUT -p tcp -m set --match-set china src -j DROP -A INPUT -p udp -m udp --dport 53 -j ACCEPT -A INPUT -p tcp -m tcp --dport 53 -j ACCEPT -A INPUT -p tcp -m tcp --dport 113 -j ACCEPT -A INPUT -p udp -m udp --dport 123 -j ACCEPT -A INPUT -p tcp -m tcp --dport 123 -j ACCEPT -A INPUT -m state --state NEW -m tcp -p tcp --dport 22 -j ACCEPT #-A INPUT -s 12.34.56.78 -j ACCEPT #-A INPUT -s yourFQDN.dyndns.org -j ACCEPT -A INPUT -p tcp -m tcp --dport 80 -j ACCEPT -A INPUT -j REJECT --reject-with icmp-host-prohibited -A FORWARD -j REJECT --reject-with icmp-host-prohibited COMMIT
Reminder: If you add another country to your block-china script, don’t forget to add a corresponding new country entry to your iptables file. See line 17 above that includes the word "china" for the syntax. There’s nothing much else to tweak except the two commented out (brown) lines that begin with #. First, remove the # symbol by moving the cursor to the right of the first one and hitting the backspace/delete key on your keyboard. Replace 12.34.56.78 with the public IP address of the computer from which you will be accessing your virtual machine. If you need multiple entries for multiple computers at different addresses, clone the line by pressing Ctrl-K and then Ctrl-U twice. Yes, we know. Some folks IP addresses change from time to time. In the next section, we’ll show you how to set up a Dynamic DNS entry with a utility that will keep track of your current IP address. In this case, uncomment the second commented line and replace yourFQDN.dyndns.org with your dynamic DNS address. Be very careful to assure that your FQDN is always on line. If the firewall cannot verify your DNS entry when it starts, the IPtables firewall will not start which means your server will be left unprotected. HINT: IP addresses are much safer because they are never verified.
Once you have your addresses configured, save the file: Ctl-X, Y, ENTER. Then issue the following commands to copy everything into place and restart the firewall.
mv /etc/sysconfig/iptables /etc/sysconfig/iptables.orig cp -p /root/iptables-lamp /etc/sysconfig/iptables echo "/etc/block-china.sh" >> /etc/rc.local /etc/block-china.sh
Always, always, always check to be sure your firewall is functioning: iptables -nL. If you don’t see your desktop computer’s public IP address near the end of the listing, then the firewall is dead. status-lamp should also show IPtables down. Check for an error message which will tell you the problematic line so you can correct it.
Implementing Dynamic DNS Service on Your Virtual Machine
There are a number of free and paid Dynamic DNS providers. The way this works is you choose a fully-qualified domain name (FQDN) to identify your computer. Then you run a dynamic DNS update utility periodically from that computer. It reports back the current public IP address of your computer and your provider updates the IP address assigned to your FQDN if it has changed. In addition to supporting sites with ever changing IP addresses, it also allows you to permanently assign an FQDN to your computer or server so that it can be accessed without using a cryptic IP address.
If that computer happens to be an Incredible PBX server or a LAMP server that you’ve set up using this tutorial, then the following will get the DNS client update utility loaded using the RPM Forge repository that we previously installed:
yum --enablerepo=rpmforge install ddclient -y
Similar DNS update clients are available for Windows, Mac OS X, and many residential routers. Then it’s just a matter of plugging in the credentials for your dynamic DNS provider and your FQDN. In the case of the CentOS client, the config file is /etc/ddclient/ddclient.conf. Now reboot your server and pick up a good book on Linux to begin your adventure.
Now For Some Fun…
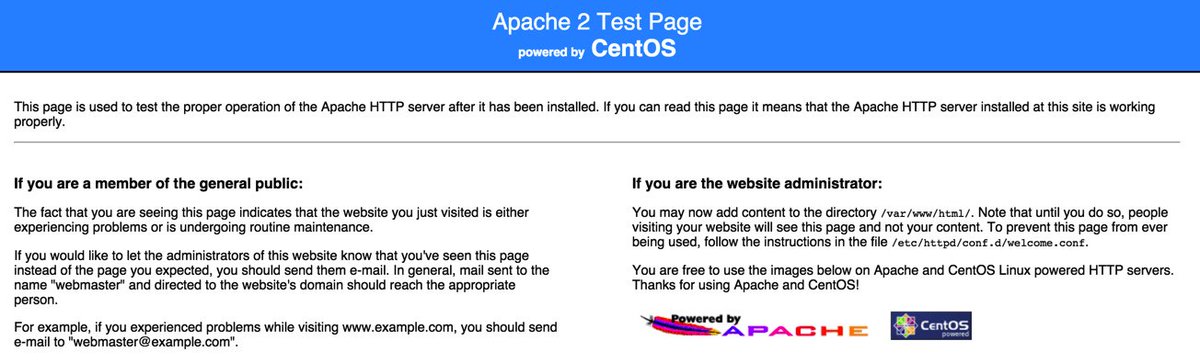
First, let’s check things out and make sure everything is working as it should. With your favorite web browser, visit the IP address of your new server. You should see the default Apache page:
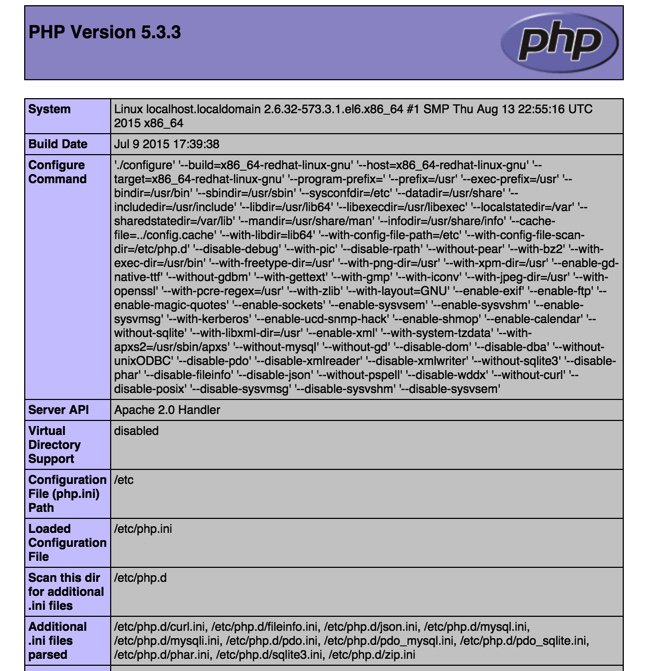
Next, let’s be sure that PHP is working as it should. While still logged into your server as root using SSH or Putty, issue the following commands and make up some file name to replace test4567 in both lines. Be sure to keep the .php file name extension. Note to gurus: Yes, we know the second line below is unnecessary if you remove the space after the less than symbol in the first line. Unfortunately, WordPress forces the space into the display which left us no alternative.
echo "< ?php phpinfo(); ?>" > /var/www/html/test4567.php sed -i 's|< |<|' /var/www/html/test4567.php
Now jump back to your web browser and access the new page you just created using the IP address of your server and the file name you made up: http://12.34.56.78/test4567.php
The PHPinfo listing will tell you everything you ever wanted to know about your web server setup including all of the PHP functions that have been enabled. That's why you want an obscure file name for the page. You obviously don't want to share that information with every bad guy on the planet. Remember. This is a public-facing web site that anyone on the Internet can access if they know or guess your IP address.
When you're ready to set up your own web site, just name it index.php and store the file in the /var/www/html directory of your server. In the meantime, issuing the following command will assure that anyone accessing your site gets a blank page until you're ready to begin your adventure:
echo " " > /var/www/html/index.php
Ready to learn PHP programming? There's no shortage of books to get you started.
Adding WordPress to Your LAMP Server
Where to begin with WordPress? What used to be a simple platform for bloggers has morphed into an all-purpose tool that makes building virtually any type of web site child's play. If you want to see what's possible, take a look at the templates and sample sites shown on WPZOOM. Unless you're an art major and savvy web designer, this will be the best $70 you ever spent. One of these templates will have your site up and running in minutes once we put the WordPress pieces in place. For the big spenders, $149 will give you access to over 50 gorgeous templates which you can download and use to your heart's content on multiple sites. And, no, your sites don't blow up after a year. You just can't download any additional templates or updates unless you renew your subscription. The other alternative is choose from thousands of templates that are provided across the Internet as well as in the WordPress application itself.
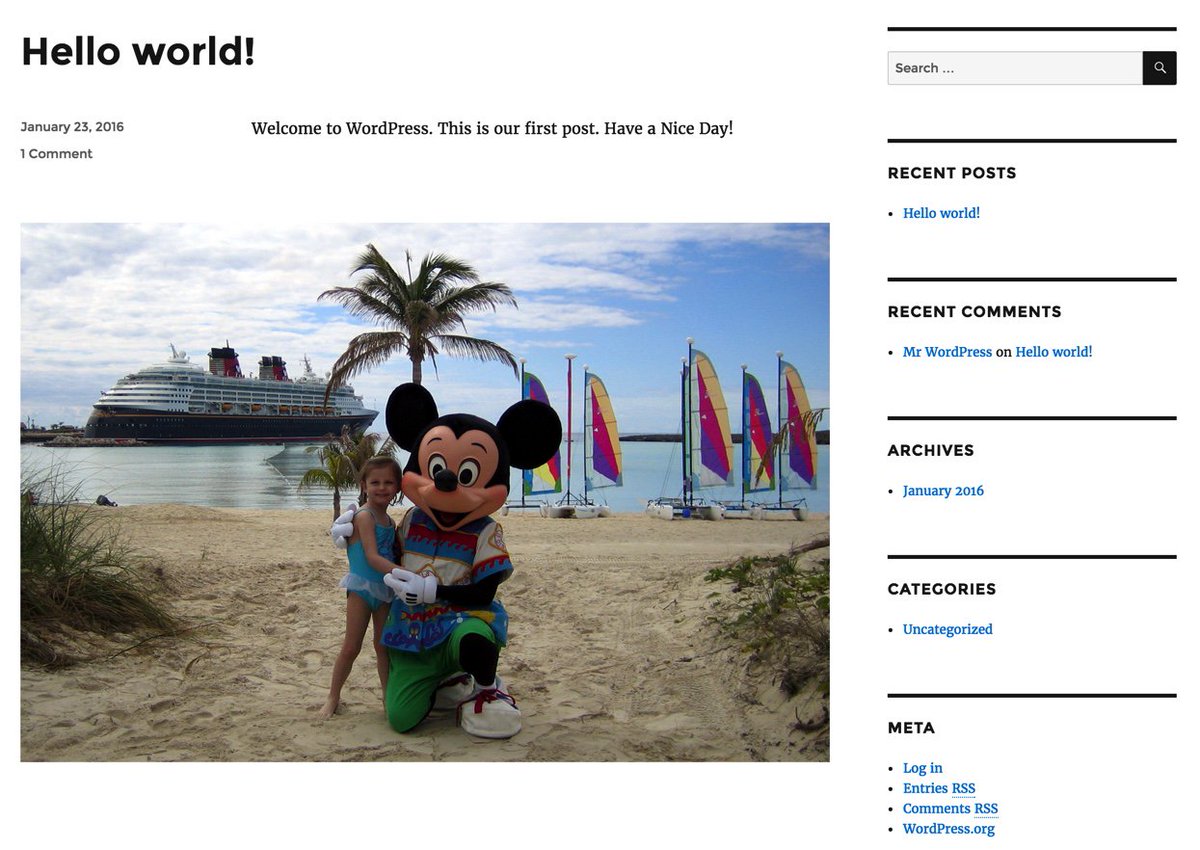
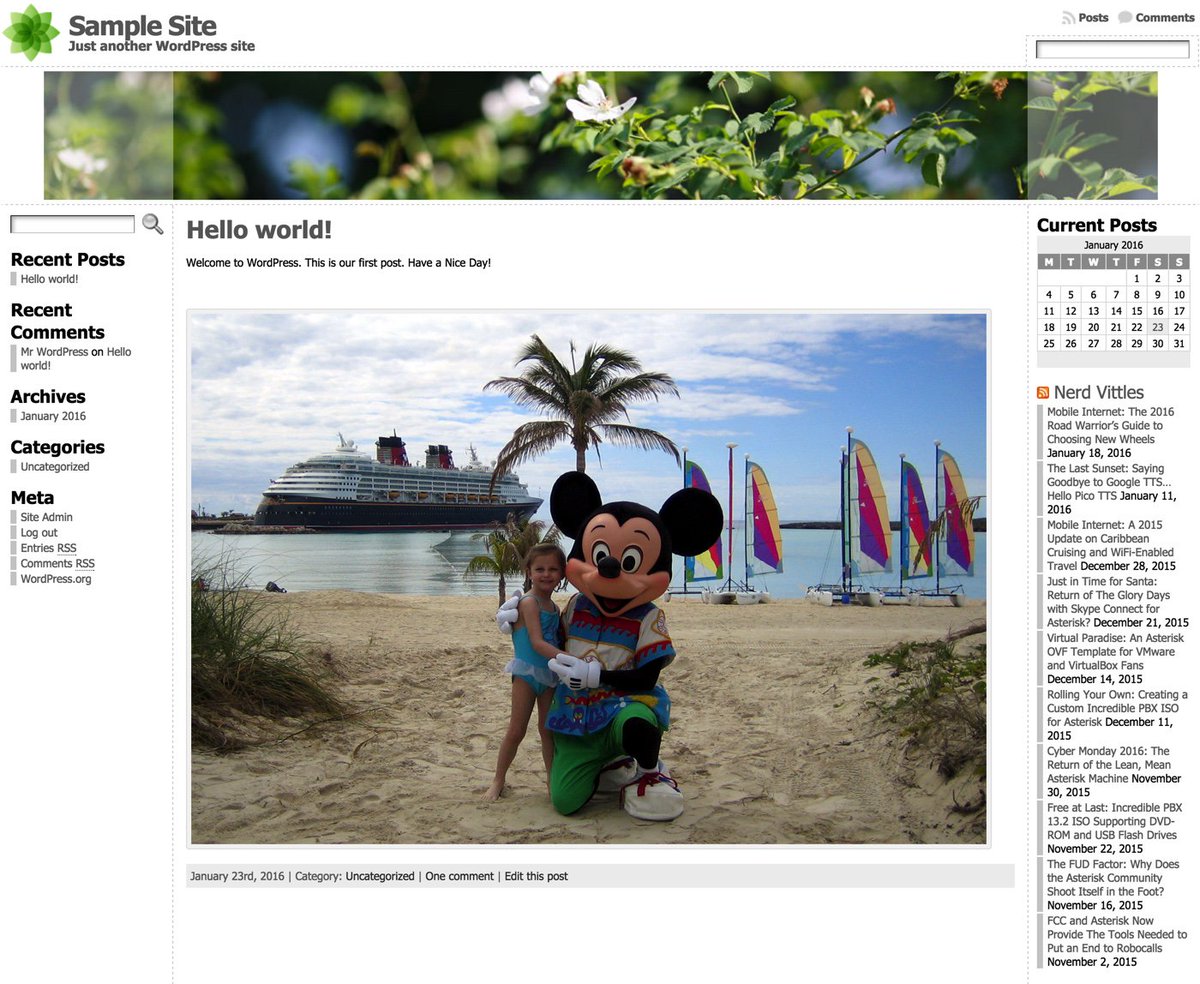
WordPress templates run the gamut from blogs to newsletters to photographer sites to e-commerce to business portfolios to video to travel to magazines to newspapers to education to food to recipes to restaurants and more. Whew! There literally is nothing you can't put together in minutes using a WordPress template. But, before you can begin, we need to get WordPress installed on your server. This is optional, of course. And, if you follow along and add WordPress, we've set it up in such a way that WordPress becomes the primary application for your site. Stated differently, when people use a browser to access your site, your WordPress template will immediately display. When we finish the basic WordPress setup and once you upload an image or two, you'll have a site that looks something like this:
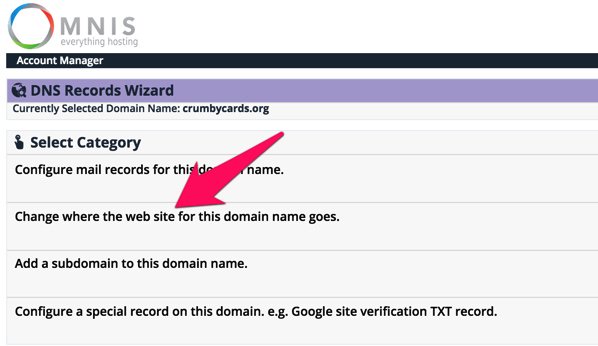
Before you begin, we strongly recommend that you acquire a domain for your site if you plan to use it for anything but experimentation. The reason is because it can be complicated to migrate a WordPress site from one location to another.2 Once you've acquired your domain, point the domain to the IP address of your new server. With a dirt cheap registrar such as Omnis.com, it's easy:
Now let's get started. To begin, we need to load the WordPress application onto your server:
cd /root mkdir wordpress cd wordpress wget http://wordpress.org/latest.tar.gz tar -xvzf latest.tar.gz -C /var/www/html
Next, we'll configure MySQL to support WordPress. We're assuming that you have NOT already created root passwords for MySQL. If you have, you'll need to add -pYourPassword to the various commands below immediately after root. There is no space between -p and your root password. Also edit the first line and make up a new password (replacing XYZ below) for the wordpress user account that will manage WordPress on your server before you cut and paste the code:
mysql -u root -e 'CREATE USER wordpress@localhost IDENTIFIED BY "XYZ";' mysql -u root -e 'CREATE DATABASE wordpress;' mysql -u root -e 'GRANT ALL ON wordpress.* TO wordpress@localhost;' mysql -u root -e 'FLUSH PRIVILEGES;'
Next, we need to configure WordPress with your new MySQL credentials. Before you cut and paste, replace XYZ in the fourth line with the password you assigned in the preceding MySQL step:
cp /var/www/html/wordpress/wp-config-sample.php /var/www/html/wordpress/wp-config.php sed -i 's|database_name_here|wordpress|' /var/www/html/wordpress/wp-config.php sed -i 's|username_here|wordpress|' /var/www/html/wordpress/wp-config.php sed -i 's|password_here|XYZ|' /var/www/html/wordpress/wp-config.php chown -R apache:apache /var/www/html/wordpress
Before you forget, take a moment and create a very secure password for your MySQL root user accounts. Here are the commands. Just replace new-password with your new password before you cut and paste. Note that you also will be prompted for this password when you execute the second command because you will now have a root user password in place from executing the first command.
/usr/bin/mysqladmin -u root password 'new-password' /usr/bin/mysqladmin -u root -p -h localhost.localdomain password 'new-password'
Finally, we need to modify your Apache web server to support WordPress as the primary application. Be sure to enter your actual email address in the third line before you cut and paste the code below:
echo " " >> /etc/httpd/conf/httpd.conf echo "" >> /etc/httpd/conf/httpd.conf echo 'ServerAdmin somebody@somedomain.com' >> /etc/httpd/conf/httpd.conf echo "DocumentRoot /var/www/html/wordpress" >> /etc/httpd/conf/httpd.conf echo "ServerName wordpress" >> /etc/httpd/conf/httpd.conf echo "ErrorLog /var/log/httpd/wordpress-error-log" >> /etc/httpd/conf/httpd.conf echo "CustomLog /var/log/httpd/wordpress-acces-log common" >> /etc/httpd/conf/httpd.conf echo " " >> /etc/httpd/conf/httpd.conf echo " " >> /etc/httpd/conf/httpd.conf service httpd restart
That should do it. Open a browser and navigate to the IP address of your server. You should be greeted with the following form. Fill in the blanks as desired. The account you're setting up will be the credentials you use to add and modify content on your WordPress site when you click Log In (as shown above). Make the username obscure and the password even more so. Remember, it's a public web site accessible worldwide! When you click Install WordPress, you'll be off to the races.
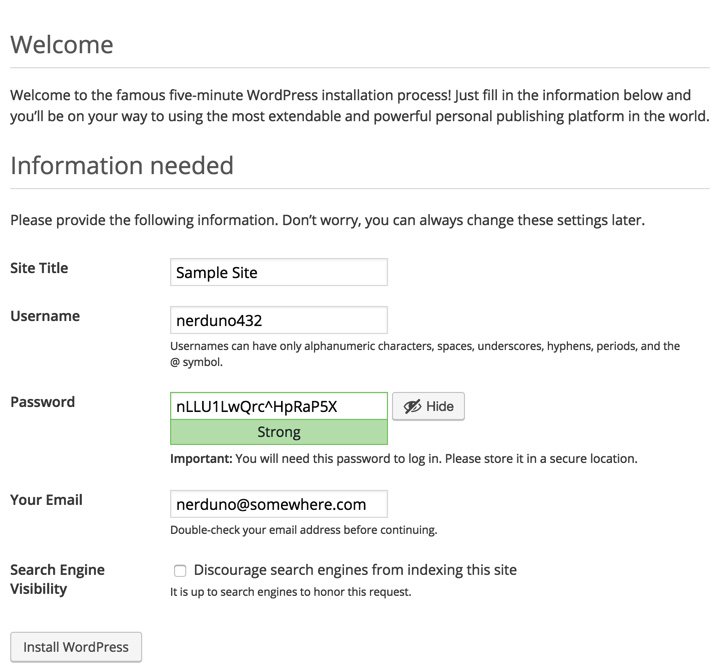
After your server whirs away for a minute or two, you will be greeted with the WordPress login prompt. With the username and password you entered above, you'll be ready to start configuring your WordPress site.

Once you're logged in, navigate to Appearance -> Themes and click Add New Theme. There's you will find literally hundreds of free WordPress templates that can be installed in a matter of seconds if WPZOOM is too rich for your blood. For a terrific all-purpose (free) theme, try Atahualpa. We'll leave our actual demo site running for a bit in case you want to explore and check out its performance. Installing and configuring the new theme took less than a minute:
A Final Word to the Wise. WordPress is relatively secure but new vulnerabilities are discovered regularly. Keep your templates, plug-ins, AND the WordPress application up to date at all times! The WordFence plug-in is a must-have. And we strongly recommend adding the following lines to your WordPress config file which then will let WordPress update everything automatically. Microsoft has given automatic updates a bad name, but in the case of WordPress, they work well.
echo "define('WP_AUTO_UPDATE_CORE', true);" >> /var/www/html/wordpress/wp-config.php
echo "add_filter( 'auto_update_plugin', '__return_true' );" >> /var/www/html/wordpress/wp-config.php
echo "add_filter( 'auto_update_theme', '__return_true' );" >> /var/www/html/wordpress/wp-config.php
Special Thanks: Our special tip of the hat goes to a few web sites that we found helpful in putting this article together especially Unixmen and Matt Wilcox & friends and Programming-Review.
Wondering What to Build Next with your new $10.50 Server in the Sky? Check out the latest Nerd Vittles tutorial. Turn it into a VoIP server FOR LIFE with free calling to/from the U.S. and Canada. Call for free demo: 
TAKE70: Build a VoIP Server in the Cloud FOR LIFE w/ Free US/CAN calling https://t.co/l9It2xq14S #asterisk #freepbx pic.twitter.com/UYuCMcfEn8
— Ward Mundy (@NerdUno) January 31, 2016
Originally published: Monday, January 25, 2016
9 Countries Have Never Visited Nerd Vittles. Got a Friend in Any of Them https://t.co/wMfmlhiQ9y #asterisk #freepbx pic.twitter.com/TPFGZbqWB6
— Ward Mundy (@NerdUno) April 22, 2016

Need help with Asterisk? Visit the PBX in a Flash Forum.
Special Thanks to Our Generous Sponsors
FULL DISCLOSURE: ClearlyIP, Skyetel, Vitelity, DigitalOcean, Vultr, VoIP.ms, 3CX, Sangoma, TelecomsXchange and VitalPBX have provided financial support to Nerd Vittles and our open source projects through advertising, referral revenue, and/or merchandise. As an Amazon Associate and Best Buy Affiliate, we also earn from qualifying purchases. We’ve chosen these providers not the other way around. Our decisions are based upon their corporate reputation and the quality of their offerings and pricing. Our recommendations regarding technology are reached without regard to financial compensation except in situations in which comparable products at comparable pricing are available from multiple sources. In this limited case, we support our sponsors because our sponsors support us.
 BOGO Bonaza: Enjoy state-of-the-art VoIP service with a $10 credit and half-price SIP service on up to $500 of Skyetel trunking with free number porting when you fund your Skyetel account. No limits on number of simultaneous calls. Quadruple data center redundancy. $25 monthly minimum spend required. Tutorial and sign up details are here.
BOGO Bonaza: Enjoy state-of-the-art VoIP service with a $10 credit and half-price SIP service on up to $500 of Skyetel trunking with free number porting when you fund your Skyetel account. No limits on number of simultaneous calls. Quadruple data center redundancy. $25 monthly minimum spend required. Tutorial and sign up details are here.
 The lynchpin of Incredible PBX 2020 and beyond is ClearlyIP components which bring management of FreePBX modules and SIP phone integration to a level never before available with any other Asterisk distribution. And now you can configure and reconfigure your new Incredible PBX phones from the convenience of the Incredible PBX GUI.
The lynchpin of Incredible PBX 2020 and beyond is ClearlyIP components which bring management of FreePBX modules and SIP phone integration to a level never before available with any other Asterisk distribution. And now you can configure and reconfigure your new Incredible PBX phones from the convenience of the Incredible PBX GUI.
 VitalPBX is perhaps the fastest-growing PBX offering based upon Asterisk with an installed presence in more than 100 countries worldwide. VitalPBX has generously provided a customized White Label version of Incredible PBX tailored for use with all Incredible PBX and VitalPBX custom applications. Follow this link for a free test drive!
VitalPBX is perhaps the fastest-growing PBX offering based upon Asterisk with an installed presence in more than 100 countries worldwide. VitalPBX has generously provided a customized White Label version of Incredible PBX tailored for use with all Incredible PBX and VitalPBX custom applications. Follow this link for a free test drive!
 Special Thanks to Vitelity. Vitelity is now Voyant Communications and has halted new registrations for the time being. Our special thanks to Vitelity for their unwavering financial support over many years and to the many Nerd Vittles readers who continue to enjoy the benefits of their service offerings. We will keep everyone posted on further developments.
Special Thanks to Vitelity. Vitelity is now Voyant Communications and has halted new registrations for the time being. Our special thanks to Vitelity for their unwavering financial support over many years and to the many Nerd Vittles readers who continue to enjoy the benefits of their service offerings. We will keep everyone posted on further developments.
Some Recent Nerd Vittles Articles of Interest...
- It doesn't take long for the probing to begin. So watch your logs, look up the IP addresses to identify the countries, and block them unless you happen to be expecting visitors from that part of the world:
[Sun Jan 24 00:36:12 2016] [error] [client 40.114.202.60] File does not exist: /var/www/html/wordpress/w00tw00t.at.blackhats.romanian.anti-sec:)[↩]
[Sun Jan 24 00:36:12 2016] [error] [client 40.114.202.60] File does not exist: /var/www/html/wordpress/phpMyAdmin
[Sun Jan 24 00:36:13 2016] [error] [client 40.114.202.60] File does not exist: /var/www/html/wordpress/phpmyadmin
[Sun Jan 24 00:36:13 2016] [error] [client 40.114.202.60] File does not exist: /var/www/html/wordpress/pma
[Sun Jan 24 00:36:13 2016] [error] [client 40.114.202.60] File does not exist: /var/www/html/wordpress/myadmin
[Sun Jan 24 00:36:14 2016] [error] [client 40.114.202.60] File does not exist: /var/www/html/wordpress/MyAdmin
[Mon Jan 25 00:29:29 2016] [error] [client 137.116.220.182] File does not exist: /var/www/html/wordpress/w00tw00t.at.blackhats.romanian.anti-sec:)
[Mon Jan 25 00:29:29 2016] [error] [client 137.116.220.182] File does not exist: /var/www/html/wordpress/phpMyAdmin
[Mon Jan 25 00:29:29 2016] [error] [client 137.116.220.182] File does not exist: /var/www/html/wordpress/phpmyadmin
[Mon Jan 25 00:29:30 2016] [error] [client 137.116.220.182] File does not exist: /var/www/html/wordpress/pma
[Mon Jan 25 00:29:30 2016] [error] [client 137.116.220.182] File does not exist: /var/www/html/wordpress/myadmin
[Mon Jan 25 00:29:30 2016] [error] [client 137.116.220.182] File does not exist: /var/www/html/wordpress/MyAdmin
- Should you ever have to migrate your WordPress site from one domain to another, here are two helpful tools to consider: the Automatic Domain Name Changer Plugin and the one we use, WordPress-Domain-Changer. [↩]
Introducing the FUD-Free Firewall for FreePBX Distro and AsteriskNOW
After frequent complaints from our FreePBX® users, we introduced a firewall application for the PBX in a Flash™ and Incredible PBX™ platforms that protected FreePBX resources. That was over 5 years ago. The product became Travelin’ Man™ 3, an IPtables-based WhiteList that totally eliminated access to your Asterisk® server unless a WhiteList entry had been authorized by the administrator. The application was further embellished over the years to facilitate access by remote users. First, we introduced PortKnocker™ for Asterisk® and later we introduced Travelin’ Man 4 to let users call in with a passcode to authorize server access. For the past several years, a preconfigured firewall has been an integral component in what has become the 7-Layer Security Model included in all Incredible PBX builds. TIP: Security is not a new idea for us.
During this evolution, the FreePBX developers introduced their own distribution, the FreePBX Distro™. Conspicuously absent was a functioning firewall. We believed that the shortcoming would be remedied quickly. Hasn’t happened! In the meantime, a number of serious security vulnerabilities arose in the FreePBX product that compromised numerous servers running their distribution because of the absence of a functioning firewall. Digium® recently reintroduced AsteriskNOW™ as a clone of the FreePBX Distro. But still no firewall.
About a month ago, we decided to close the loophole for everyone’s security and develop a firewall for the only FreePBX-based distributions without a firewall, the FreePBX Distro and AsteriskNOW. Last week we began the rollout with a Nerd Vittles article explaining why this was essential, as if an explanation were necessary. Today, you get the GPL code.
Suffice it to say, our article was not well received. The usual Sangoma® players went into Damage Control Mode with what has become a predictable scenario whenever security issues are raised concerning the FreePBX design or vulnerabilities.
Meet The Sangoma 7.
- The Good Cop: If only you’d purchase Genuine Sangoma Hardware, all of your security problems would disappear
- The Bad Cop: Enjoy this nice Cup of FUD about your own distro which proves we’re all just alike
- The Techie Cop: We thought of developing an open source firewall just the other day, and now you’re complaining
- The Rest of "The Team": Let the Astroturfing Begin… Retweet, favorite, and cheer for the brilliance of My 3 Cops
The Good Cop offered to solve all your security woes if you’d just buy (some more Sangoma) hardware.
The Bad Cop suggested that, with "cookie cutter security, you might as well hand out your password." Just in case you have any doubts about whose approach has stood the test of time, let’s Google the FreePBX Security Vulnerability Track Record.
The Techie Cop claimed we had stolen his 2-day old idea to create an Open Source Firewall. Really?
Earth to Techie Cop: Where have you been for the past five years??
Funny stuff… if it weren’t so damaging to the Asterisk community and those trying to decide whether to put their faith in open source communications software.
Firewall Basics.
We’ve written dozens of articles on Asterisk security and firewall approaches so we won’t repeat all of the information. Here’s what you need to know. Software-based firewalls on Linux servers need to be integrated into the Linux kernel to be secure. IPtables is kernel-based and extremely reliable. Blacklist-based firewall designs, i.e. those that seek to identify the IP addresses of every bad guy on the planet don’t work very well. Bad guys aren’t stupid. They can do their damage by commandeering a little old lady’s Windows machine so you’re never going to collect all of the necessary "bad" IP addresses. They’re also smart enough to poison the blacklists with Internet resources you need such as DNS servers. So don’t waste your time with blacklists. WhiteLists work very well. You identify the IP addresses and FQDNs of all the Internet sites you need to support and all the SIP providers you wish to use. Nobody else even sees your server on the Internet. If the bad guys can’t see your server, they can’t attack it. Simple as that.
Travelin’ Man 3 WhiteList Tutorial.
Here are the fundamentals of the Travelin’ Man 3 design. We allow access from anybody and everybody on your private LAN. They still need a password to access FreePBX or to gain root access, but they can "see" your server. Private LAN addresses are non-routable over the Internet which means the bad guys can’t access your 192.168.0.4 IP address if you’re sitting behind a NAT-based hardware firewall. All of your internal phones will work with no firewall modifications. You may need to adjust these settings if you’re using a Cloud resource such as Amazon because they actually route non-routable IP addresses which would leave your server vulnerable without removing these entries (especially the 172 subnet for Amazon):
#-A INPUT -s 10.0.0.0/8 -j ACCEPT #-A INPUT -s 172.16.0.0/12 -j ACCEPT #-A INPUT -s 192.168.0.0/16 -j ACCEPT
Travelin’ Man 3 also authorizes access for certain mandatory services that are needed to keep your server operating properly. In addition, during installation, Travelin’ Man 3 whitelists localhost and the public and private IP addresses of your server as well as your PC or workstation. You obviously don’t want to lock yourself out of your own server.
As of today, Travelin’ Man 3 is primarily an IPv4 whitelist toolkit. IPv6 addresses are only supported to allow localhost access to your server. Any other IPv6 addresses must be added manually in /etc/sysconfig/ip6tables. We recommend not using FQDNs with IPv6 for the time being. And always restart IP6tables after adding new entries: service ip6tables restart.
You have the option of enabling the Incredible PBX collection of IP addresses used by many of the leading SIP providers around the world. Just run the enable-trusted-providers script in /root. The list of included providers is available here. You also have the option of adding (whitelisting) or deleting users’ and providers’ IP addresses and FQDNs yourself. Use the included scripts in the /root folder: add-ip, add-fqdn, and del-acct. For each account you set up, you get to define which access permission or combination of permissions will be available:
0 – ALL Services
1 – SIP (UDP)
2 – SIP (TCP)
3 – IAX
4 – Web
5 – WebMin
6 – FTP
7 – TFTP
8 – SSH
9 – FOP
Once you have made your selection, a user account will be created in /root with the name of the account and an extension of .iptables. Do NOT delete these files. They keep track of current IP addresses and accounts authorized for server access.
If you have remote users on the Internet, e.g. traveling salespeople, you can individually authorize access for them using a dynamic FQDN (add-fqdn) coupled with a dynamic DNS server that keeps IP addresses current as folks move around. Just load a dynamic DNS updater on their smartphone. Then plug the user entries into the included ipchecker script and execute a cron job on your server every few minutes to keep the FQDN entries refreshed. Simple.
echo "*/10 * * * * root /root/ipchecker > /dev/null 2>&1" >> /etc/crontab
IPtables does not directly support FQDN rules through the kernel. However, IPtables lets you configure your firewall rules using FQDNs which get translated into IP addresses whenever IPtables is restarted. The gotcha here is that, if an FQDN is not resolvable, IPtables fails to load, and you’re left with a vulnerable server. Travelin’ Man 3 takes care of this by employing a special restart script that temporarily disables unresolvable IP addresses.
The moral of the story:
ALWAYS USE iptables-restart TO RELOAD IPTABLES OR YOUR SERVER MAY END UP WITH NO FIREWALL!
We’ve also included support for a neat little trick that lets you whitelist remote SIP access to your server using a special FQDN. No further firewall adjustments are necessary. This is supported on most platforms except OpenVZ containers. The way this works is you first assign an obscure FQDN to your server’s IP address. It needs to be obscure because anyone with the FQDN gains SIP access to your server. But chances are pretty good that the bad guys will have a hard time figuring out that xq356jq.dyndns.org points to your server. You then can embed this FQDN in the SIP phone credentials for all of your remote users. The final step is to uncomment the last few lines in /etc/sysconfig/iptables after plugging in your obscure FQDN. Then restart IPtables: iptables-restart.
-A INPUT -p udp --dport 5060:5061 -m string --string "REGISTER sip:xq356jq.dyndns.org" --algo bm -j ACCEPT -A INPUT -p udp --dport 5060:5061 -m string --string "REGISTER sip:" --algo bm -j DROP -A INPUT -p udp --dport 5060:5061 -m string --string "OPTIONS sip:" --algo bm -j DROP
Finally, a word of caution about deploying Travelin’ Man 3 on the FreePBX Distro and AsteriskNOW platforms. We currently don’t have a vehicle in place to push security updates out to you as we do with Incredible PBX. This means you will have to remain vigilant to what’s happening in the telecommunications world and load updates yourself. You can stay current in a number of ways. We will post updates to this article in comments below so you can simply check back here periodically. An easier way to keep up with the latest security alerts and updates is to subscribe to the PBX in a Flash RSS Feed. This can be added to the FreePBX Status page by editing RSS Feeds in Settings -> Advanced Settings and adding:
http://pbxinaflash.com/rssfeed.xml
As you can see, there’s nothing "cookie cutter" about Travelin’ Man 3. It’s totally customizable to meet your own unique requirements. All we have done is tame IPtables and eliminate much of its complexity so that you can get a functional firewall up and running quickly. Now it’s deployment time!
Installing Travelin’ Man 3 for the FreePBX Distro & AsteriskNOW.
Log into your server as root from a desktop PC using SSH or Putty. This assures that you will have access from a device other than the console when you are finished. Then issue the following commands:
cd /root wget http://incrediblepbx.com/tm3-firewall.tar.gz tar zxvf tm3-firewall.tar.gz ./enable-iptables-whitelist
If you wish to enable the Incredible PBX trusted providers whitelist, issue the following command:
./enable-trusted-providers
ALWAYS use the following command to start or restart IPtables:
iptables-restart
NEVER use the following syntax with Travelin’ Man 3:
service iptables...
CHECK the status of your server at any time:
/root/status
The GPL Is NOT Dead: Coming Soon to FreePBX Distro and AsteriskNOW…
Stay tuned for Incredible PBX GUI, all of the GPL modules you know and love with NO NAGWARE and NO GOTCHAS. This also will assist users that got duped by the Sangoma offer to convert PBX in a Flash into a proprietary FreePBX Distro. ![]() After reading the Sangoma disclaimer about the script being donated by an anonymous user, ask yourself this question. When was the last time Sangoma republished code that they did not own or create themselves? Try NEVER.
After reading the Sangoma disclaimer about the script being donated by an anonymous user, ask yourself this question. When was the last time Sangoma republished code that they did not own or create themselves? Try NEVER.
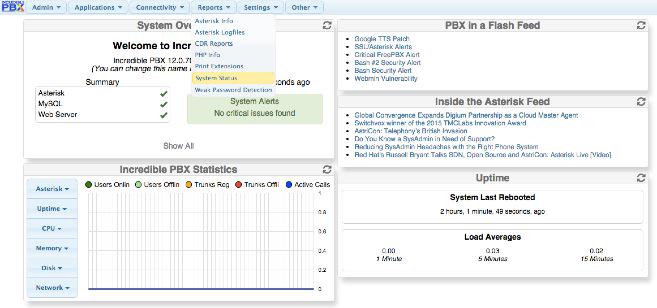
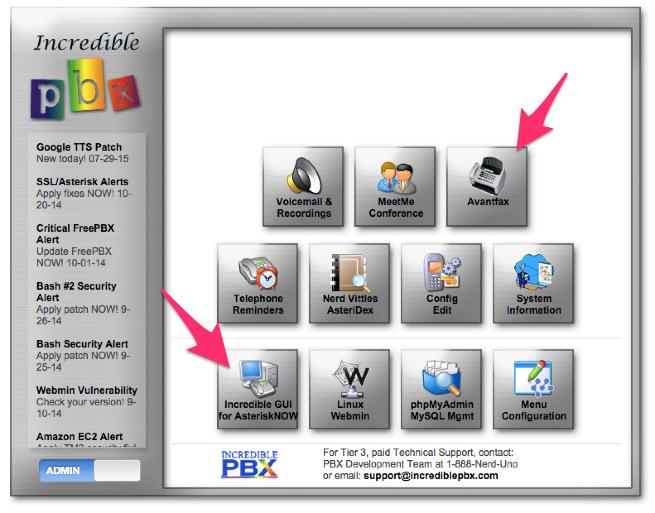
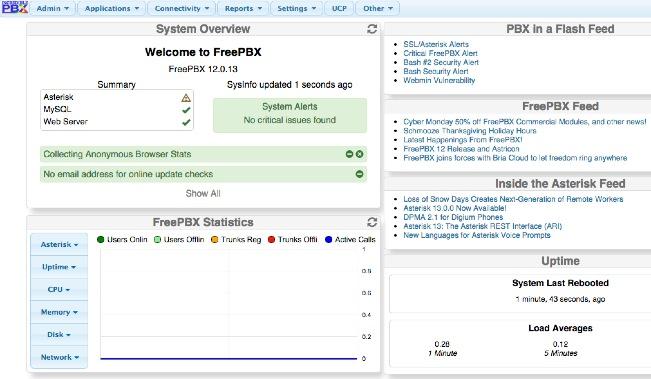
BEFORE:
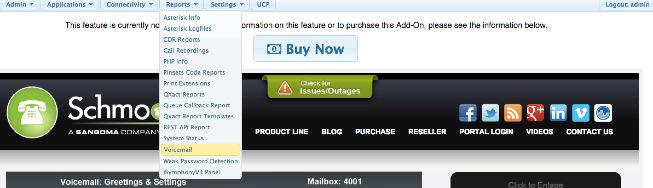
AFTER:
Originally published: Monday, August 10, 2015

Need help with Asterisk? Visit the PBX in a Flash Forum.
Special Thanks to Our Generous Sponsors
FULL DISCLOSURE: ClearlyIP, Skyetel, Vitelity, DigitalOcean, Vultr, VoIP.ms, 3CX, Sangoma, TelecomsXchange and VitalPBX have provided financial support to Nerd Vittles and our open source projects through advertising, referral revenue, and/or merchandise. As an Amazon Associate and Best Buy Affiliate, we also earn from qualifying purchases. We’ve chosen these providers not the other way around. Our decisions are based upon their corporate reputation and the quality of their offerings and pricing. Our recommendations regarding technology are reached without regard to financial compensation except in situations in which comparable products at comparable pricing are available from multiple sources. In this limited case, we support our sponsors because our sponsors support us.
 BOGO Bonaza: Enjoy state-of-the-art VoIP service with a $10 credit and half-price SIP service on up to $500 of Skyetel trunking with free number porting when you fund your Skyetel account. No limits on number of simultaneous calls. Quadruple data center redundancy. $25 monthly minimum spend required. Tutorial and sign up details are here.
BOGO Bonaza: Enjoy state-of-the-art VoIP service with a $10 credit and half-price SIP service on up to $500 of Skyetel trunking with free number porting when you fund your Skyetel account. No limits on number of simultaneous calls. Quadruple data center redundancy. $25 monthly minimum spend required. Tutorial and sign up details are here.
 The lynchpin of Incredible PBX 2020 and beyond is ClearlyIP components which bring management of FreePBX modules and SIP phone integration to a level never before available with any other Asterisk distribution. And now you can configure and reconfigure your new Incredible PBX phones from the convenience of the Incredible PBX GUI.
The lynchpin of Incredible PBX 2020 and beyond is ClearlyIP components which bring management of FreePBX modules and SIP phone integration to a level never before available with any other Asterisk distribution. And now you can configure and reconfigure your new Incredible PBX phones from the convenience of the Incredible PBX GUI.
 VitalPBX is perhaps the fastest-growing PBX offering based upon Asterisk with an installed presence in more than 100 countries worldwide. VitalPBX has generously provided a customized White Label version of Incredible PBX tailored for use with all Incredible PBX and VitalPBX custom applications. Follow this link for a free test drive!
VitalPBX is perhaps the fastest-growing PBX offering based upon Asterisk with an installed presence in more than 100 countries worldwide. VitalPBX has generously provided a customized White Label version of Incredible PBX tailored for use with all Incredible PBX and VitalPBX custom applications. Follow this link for a free test drive!
 Special Thanks to Vitelity. Vitelity is now Voyant Communications and has halted new registrations for the time being. Our special thanks to Vitelity for their unwavering financial support over many years and to the many Nerd Vittles readers who continue to enjoy the benefits of their service offerings. We will keep everyone posted on further developments.
Special Thanks to Vitelity. Vitelity is now Voyant Communications and has halted new registrations for the time being. Our special thanks to Vitelity for their unwavering financial support over many years and to the many Nerd Vittles readers who continue to enjoy the benefits of their service offerings. We will keep everyone posted on further developments.
Some Recent Nerd Vittles Articles of Interest…
Firewalls 101: Why Every Asterisk Server Should Have a Functioning Firewall
Part of our fundamental disagreement with the FreePBX® design can be summed up in one word: FIREWALL or the lack of a functioning firewall in the FreePBX Distro and in the functionally identical Digium product, AsteriskNOW®.1 Most of the other design choices including the controversial, non-GPL compliant Module Signature Checking mechanism are touted as failsafe ways to detect altered systems even though changes in FreePBX MySQL tables and Asterisk config files can be modified easily without triggering alerts. In short, the Band-Aid® approach to module tampering does nothing to address the fundamental problem, prevention of unauthorized intrusions in the first place.
Some would contend that the included Fail2Ban product is specifically designed to prevent unauthorized intrusions by locking out the bad guys after a certain number of failed login attempts. Assuming Fail2Ban were functioning properly, which does not appear to be the case, putting all your eggs in the Fail2Ban basket also ignores several critical shortcomings in Fail2Ban. First, it has been documented that powerful servers such as Amazon EC2 and Twitter botnets give hackers almost unlimited intrusion attempts before Fail2Ban ever gets a time slice sufficient to scan logs for intrusion attempts. Second, Fail2Ban provides no protection against stealthy distributed bruteforcing activity. For example, if a botnet with 770,000 PCs attacked your server and each PC executed only two login attempts, Fail2Ban never gets triggered even assuming your server could handle the load and Fail2Ban got sufficient server resources to actually scan your logs. Finally, Fail2Ban provides no protection against Zero Day vulnerabilities where an intruder basically walks right into your server because of an unidentified vulnerability lurking in the existing code. Unfortunately, these are not hypothetical situations but regular occurrences over the past 10 years of Asterisk and FreePBX development. In a nutshell, that’s why you need a real firewall. It completely blocks all access to your server by unauthorized users all of the time.
Numerous companies have intentionally exposed Asterisk® servers to the public Internet in a continuing effort to identify problems before they affect "real servers." We know of no similar efforts with a platform that includes FreePBX as an integral component of the server. Why? Because the potential for Zero Day Vulnerabilities in a platform of modular design is enormous. One vulnerable component in FreePBX and the entire house of cards collapses because of the blank check server access that a compromised FreePBX asterisk user account gives to an intruder. It’s the fundamental reason that services such as Apache were engineered to run with different user credentials than a root user in the real world. In essence, the current FreePBX design with Asterisk has elevated asterisk user credentials to allow root-like access to almost every server file and function with the exception of SSH access. And SSH access becomes all but unnecessary given the scope of the GUI functionality provided within FreePBX and the escalated privileges it enjoys.
On FreePBX-based Asterisk servers, the absence of any user account separation means Asterisk, Apache, and FreePBX services all operate under the single asterisk user account. If any piece collapses due to a vulnerability, the intruder gets the keys to the castle including read/write access to Asterisk and FreePBX manager credentials and config files as well as broad MySQL access. This, in turn, exposes your VoIP account credentials in addition to facilitating SQL injection into any and all FreePBX database tables. Because FreePBX "hides" numerous settings in over a hundred MySQL tables, the Asterisk DB, and dozens of Asterisk config files, once the asterisk user account access is compromised, many of the major components on your server could be cleverly reconfigured without leaving much of a hint that your server had been compromised. In fact, VoIP account credentials could be extracted and used elsewhere with no traceable footprint back to your server. For all you would know, your provider compromised your credentials rather than the other way around. Just another reminder that keeping a credit card on file for automatic replenishment with VoIP providers is a very bad idea!
Providing the asterisk user with these broad permissions was a (poor) design choice. Why was it done? To make it easy for the developers to alter virtually everything on your Asterisk server using FreePBX’s integrated Module Admin component. Root user permissions are never required to do much of anything other than server platform upgrades once the FreePBX Distro or AsteriskNOW product is installed. That’s exactly the design one would expect to find in a commercial, closed source software platform. But it’s unusual in the open source community to put it charitably. We trust we’ve made the case why a rock-solid firewall with any product that uses FreePBX modules is absolutely essential. FreePBX is a wonderful GUI, but use of the platform without a properly configured, fully functional firewall could be financially catastrophic not to mention the serious damage it could cause to others including the good reputation of Asterisk in the Internet community.

Our objective next week will be to help you implement a functioning Linux-based software firewall on the FreePBX Distro and AsteriskNOW platforms. It’s FREE! Not only will this improve the security of your server, but it will deny the bad guys a platform from which to launch mischievous acts against the rest of us. Unless you’re running Asterisk on a Cloud-based platform, do all of us a favor NOW! Run, don’t walk, to your nearest electronics store (including WalMart and BestBuy) and purchase one of the dozens of inexpensive NAT-based routers. Install it between the Internet and your server TODAY! This is the one we use, but there are plenty from which to choose including our refurbished one.2
NEWS FLASH: Download the new FUD-Free Firewall for FreePBX Distro and AsteriskNOW.
Originally published: Monday, August 3, 2015

Need help with Asterisk? Visit the PBX in a Flash Forum.
Special Thanks to Our Generous Sponsors
FULL DISCLOSURE: ClearlyIP, Skyetel, Vitelity, DigitalOcean, Vultr, VoIP.ms, 3CX, Sangoma, TelecomsXchange and VitalPBX have provided financial support to Nerd Vittles and our open source projects through advertising, referral revenue, and/or merchandise. As an Amazon Associate and Best Buy Affiliate, we also earn from qualifying purchases. We’ve chosen these providers not the other way around. Our decisions are based upon their corporate reputation and the quality of their offerings and pricing. Our recommendations regarding technology are reached without regard to financial compensation except in situations in which comparable products at comparable pricing are available from multiple sources. In this limited case, we support our sponsors because our sponsors support us.
 BOGO Bonaza: Enjoy state-of-the-art VoIP service with a $10 credit and half-price SIP service on up to $500 of Skyetel trunking with free number porting when you fund your Skyetel account. No limits on number of simultaneous calls. Quadruple data center redundancy. $25 monthly minimum spend required. Tutorial and sign up details are here.
BOGO Bonaza: Enjoy state-of-the-art VoIP service with a $10 credit and half-price SIP service on up to $500 of Skyetel trunking with free number porting when you fund your Skyetel account. No limits on number of simultaneous calls. Quadruple data center redundancy. $25 monthly minimum spend required. Tutorial and sign up details are here.
 The lynchpin of Incredible PBX 2020 and beyond is ClearlyIP components which bring management of FreePBX modules and SIP phone integration to a level never before available with any other Asterisk distribution. And now you can configure and reconfigure your new Incredible PBX phones from the convenience of the Incredible PBX GUI.
The lynchpin of Incredible PBX 2020 and beyond is ClearlyIP components which bring management of FreePBX modules and SIP phone integration to a level never before available with any other Asterisk distribution. And now you can configure and reconfigure your new Incredible PBX phones from the convenience of the Incredible PBX GUI.
 VitalPBX is perhaps the fastest-growing PBX offering based upon Asterisk with an installed presence in more than 100 countries worldwide. VitalPBX has generously provided a customized White Label version of Incredible PBX tailored for use with all Incredible PBX and VitalPBX custom applications. Follow this link for a free test drive!
VitalPBX is perhaps the fastest-growing PBX offering based upon Asterisk with an installed presence in more than 100 countries worldwide. VitalPBX has generously provided a customized White Label version of Incredible PBX tailored for use with all Incredible PBX and VitalPBX custom applications. Follow this link for a free test drive!
 Special Thanks to Vitelity. Vitelity is now Voyant Communications and has halted new registrations for the time being. Our special thanks to Vitelity for their unwavering financial support over many years and to the many Nerd Vittles readers who continue to enjoy the benefits of their service offerings. We will keep everyone posted on further developments.
Special Thanks to Vitelity. Vitelity is now Voyant Communications and has halted new registrations for the time being. Our special thanks to Vitelity for their unwavering financial support over many years and to the many Nerd Vittles readers who continue to enjoy the benefits of their service offerings. We will keep everyone posted on further developments.
Some Recent Nerd Vittles Articles of Interest…
- Technically, IPtables is running on the FreePBX Distro and AsteriskNOW platforms; however, it’s sole function is to act as the shutdown mechanism for Fail2Ban-detected breaches. It does not independently examine packets. There is no functioning iptables config file. From our vantage point, serving as the Fail2Ban traffic cop doesn’t qualify as a functioning firewall since it lacks any of the traditional IPtables rules that manage PREROUTING, INPUT, FORWARD, OUTPUT, and POSTROUTING of packets. [↩]
- Where prices are competitive or availability is a factor, we often recommend Amazon because Amazon provides financial support to Nerd Vittles through our referral links. We encourage everyone to shop independently and purchase products from suppliers that best meet your own requirements. [↩]
Firewalls and Internet Security: Separating FUD and Fiction in the VoIP World
Some of us have spent years developing secure VoIP solutions for Asterisk® that protect your phone bill while bringing Cloud-based solutions within reach of virtually anyone. So it’s particularly disappointing when a hardware manufacturer spreads fear, uncertainty, and doubt in order to peddle their hardware. In this case, it happens to be Session Border Controllers (SBCs). We want you to watch this latest "infomercial" for yourself:
https://youtu.be/Bp_7m64k_ko
To hear Sangoma tell it, every VoIP server protected by merely a firewall is vulnerable to endless SIP attacks unless, of course, you purchase an SBC. And since implementation of Cloud-based servers traditionally limits the ability to deploy an SBC, most Cloud-based VoIP solutions would become vulnerable to SIP attacks. In the words of Sangoma:
And with telecom fraud and PBX hacking on the rise, it’s important to keep your network secure. For most enterprises, it’s not a matter of if-but-when their [sic] network experiences an attack, potentially costing you valuable time and money.
Now Sangoma is touting an article in a blog from the U.K. that begins with the headline "Why Firewalls are not Enough." The purported author is Jack Eagle, who is otherwise unidentified. Not surprisingly, the owner of the blog happens to be a reseller of Sangoma hardware. Here’s what Jack Eagle suggests:
In addition, the inherent function of firewalls is to deny all unsolicited traffic. Whereby, the act of making a phone call is an unsolicited event, thus, firewalls can be counterproductive to an effective VoIP deployment by denying VoIP traffic.
For the benefit of those of you considering a VoIP deployment either locally or in the Cloud using Asterisk, let’s cut to the chase and directly address some of the FUD that’s been thrown out there.
FUD #1: Internet SIP Access Exposes Asterisk to Attack
False. What is true is that unrestricted SIP access to your server from the Internet without a properly secured firewall may expose Asterisk to attack. Perhaps it’s mere coincidence but the only major Asterisk aggregation that still installs Asterisk with an unsecured firewall and no accompanying script, tutorial, or even recommendation to properly lock it down and protect against SIP attacks happens to be from the same company that now wants you to buy a session border controller.
FUD #2: Firewalls Aren’t Designed to Protect Asterisk from SIP Attacks
False. What is true is that the base firewall installation provided in the FreePBX® Distro does not protect against any attacks. In a Cloud-based environment or with local deployments directly exposed to the Internet, that could very well spell disaster. And it has on a number of occasions. The Linux IPtables firewall is perfectly capable of insulating your Asterisk server from SIP attacks when properly configured. With PBX in a Flash and its open source Travelin’ Man 3 script, anonymous SIP access is completely eliminated. The same is true using the tools provided in the latest Elastix servers. And, Incredible PBX servers have always included a secured firewall with simple tools to manage it. Of course, with local VoIP hardware and a hardware-based firewall, any Asterisk server can be totally insulated from SIP attacks whether IPtables is deployed or not. Just don’t open any ports in your firewall and register your trunks with your SIP providers. Simple as that.
FUD #3: SIP Provider Access to Asterisk Compromises Your Firewall
False. Registering a server with SIP or IAX trunk providers is all that is required to provide secure VoIP communications. Calls can flow in and out of your Asterisk PBX without compromising your server or communications in any way. Contrary to what is depicted in the infomercial, there is no need to poke a hole in your firewall to expose SIP traffic. In fact, we know of only one SIP provider that requires firewall changes in order to use their services. Simple answer: use a different provider. Consider how you access Internet sites with a browser from behind a firewall. The connection from your browser to web sites on the Internet can be totally secure without any port exposure in your firewall configuration. Registering a SIP trunk with a SIP provider accomplishes much the same thing. All modern firewalls and routers will automatically handle the opening and closing of ports to accommodate the SIP or IAX communications traffic.
FUD #4: Remote Users Can’t Access Asterisk Without SIP Exposure
False. Over the past several years, we have written about a number of methodologies which allow remote users to securely access an Asterisk server. That’s what Virtual Private Networks and Port Knocking and Remote Firewall Management are all about. All of these solutions provide access without exposing your server to any SIP vulnerabilities! We hope the authors of this infomercial will give these open source tools a careful look before tarnishing the VoIP brand by suggesting vulnerabilities which any prudent VoIP deployment can easily avoid without additional cost. Just use the right products!
Originally published: Thursday, April 23, 2015

Need help with Asterisk? Visit the PBX in a Flash Forum.
Special Thanks to Our Generous Sponsors
FULL DISCLOSURE: ClearlyIP, Skyetel, Vitelity, DigitalOcean, Vultr, VoIP.ms, 3CX, Sangoma, TelecomsXchange and VitalPBX have provided financial support to Nerd Vittles and our open source projects through advertising, referral revenue, and/or merchandise. As an Amazon Associate and Best Buy Affiliate, we also earn from qualifying purchases. We’ve chosen these providers not the other way around. Our decisions are based upon their corporate reputation and the quality of their offerings and pricing. Our recommendations regarding technology are reached without regard to financial compensation except in situations in which comparable products at comparable pricing are available from multiple sources. In this limited case, we support our sponsors because our sponsors support us.
 BOGO Bonaza: Enjoy state-of-the-art VoIP service with a $10 credit and half-price SIP service on up to $500 of Skyetel trunking with free number porting when you fund your Skyetel account. No limits on number of simultaneous calls. Quadruple data center redundancy. $25 monthly minimum spend required. Tutorial and sign up details are here.
BOGO Bonaza: Enjoy state-of-the-art VoIP service with a $10 credit and half-price SIP service on up to $500 of Skyetel trunking with free number porting when you fund your Skyetel account. No limits on number of simultaneous calls. Quadruple data center redundancy. $25 monthly minimum spend required. Tutorial and sign up details are here.
 The lynchpin of Incredible PBX 2020 and beyond is ClearlyIP components which bring management of FreePBX modules and SIP phone integration to a level never before available with any other Asterisk distribution. And now you can configure and reconfigure your new Incredible PBX phones from the convenience of the Incredible PBX GUI.
The lynchpin of Incredible PBX 2020 and beyond is ClearlyIP components which bring management of FreePBX modules and SIP phone integration to a level never before available with any other Asterisk distribution. And now you can configure and reconfigure your new Incredible PBX phones from the convenience of the Incredible PBX GUI.
 VitalPBX is perhaps the fastest-growing PBX offering based upon Asterisk with an installed presence in more than 100 countries worldwide. VitalPBX has generously provided a customized White Label version of Incredible PBX tailored for use with all Incredible PBX and VitalPBX custom applications. Follow this link for a free test drive!
VitalPBX is perhaps the fastest-growing PBX offering based upon Asterisk with an installed presence in more than 100 countries worldwide. VitalPBX has generously provided a customized White Label version of Incredible PBX tailored for use with all Incredible PBX and VitalPBX custom applications. Follow this link for a free test drive!
 Special Thanks to Vitelity. Vitelity is now Voyant Communications and has halted new registrations for the time being. Our special thanks to Vitelity for their unwavering financial support over many years and to the many Nerd Vittles readers who continue to enjoy the benefits of their service offerings. We will keep everyone posted on further developments.
Special Thanks to Vitelity. Vitelity is now Voyant Communications and has halted new registrations for the time being. Our special thanks to Vitelity for their unwavering financial support over many years and to the many Nerd Vittles readers who continue to enjoy the benefits of their service offerings. We will keep everyone posted on further developments.
Some Recent Nerd Vittles Articles of Interest…
Midnight Madness: Introducing Incredible PBX 12 with Asterisk 12 and FreePBX
[iframe-popup id="4″]
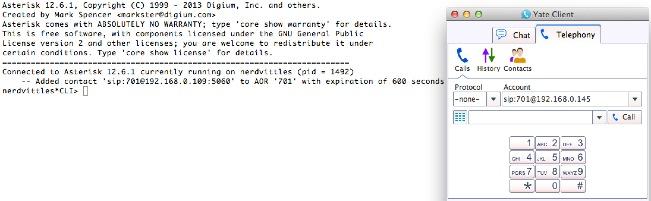
The number "12″ always has held mystical prominence in our culture and so it is with Asterisk®. Just over 12 months ago, Digium first introduced Asterisk 12 at AstriCon in Atlanta and heralded a major change in the direction of the product. It was more than a wholesale revamping of the Asterisk feature set. There was a revolutionary new development methodology thanks to the untiring efforts of Matt Jordan and his incredibly talented development team. Unlike Asterisk releases of old, there were no serious breakages in existing applications and, where there were changes, they were carefully documented for all the world to see. Thank you, Matt & Co.
The release of Asterisk 12 also set in motion the development of FreePBX® 12 by the equally talented FreePBX Dev Team. What began as an effort simply to integrate all of the new components in Asterisk 12 quickly evolved into a major rewrite of the graphical user interface for Asterisk, no small feat given its history of starts and stops spanning nearly a decade of development. Just last week, FreePBX 12 was pronounced stable and production ready. If you thought Asterisk 12 was revolutionary, just wait until you try FreePBX 12. Simply amazing work by the FreePBX Development Team. Thank you.
While PBX in a Flash has offered a preview edition of Asterisk 12 and FreePBX 12 for quite a while, we’ve held off releasing the stand-alone Incredible PBX 12 for a number of reasons. First and foremost, we wanted Incredible PBX 12 to remain pure open source to point the way for others that want to enhance Asterisk 12 and FreePBX 12. Second, there were more than a few rough edges with both products that simply needed some time to evolve. The one year anniversary of Asterisk 12 and the stable release of FreePBX 12 seemed a fitting occasion to add our turnkey implementation of Incredible PBX to the mix.
The real beauty of Incredible PBX: there is no smoke and there are no mirrors. What you see is what you get. You begin with a base install of the Linux operating system. And then the open source Incredible PBX installer adds all of the pieces to integrate air-tight security with Asterisk 12, FreePBX 12, text-to-speech technology and dozens of applications for Asterisk into a seamless platform for either experimentation or production use. You can review the source code and embellish it as you see fit! Protecting your deployment is the IPtables firewall with a WhiteList for authorized user access coupled with Fail2Ban to monitor access attempts. This isn’t merely a security toolkit. Your server is actually locked down from the moment you complete the Incredible PBX install. Authorizing additional users is accomplished using simple administrator scripts. Or end-users can employ PortKnocker and Travelin’ Man 4 to simplify remote access. Automatic updates for security fixes and enhancements are an integral component of Incredible PBX. If the security alerts of the past month haven’t convinced you that updates are critically important, you probably should stop hosting your own PBX. Backups and restores also are simple. And the complete open source feature set of both Asterisk and FreePBX is activated to facilitate your development efforts. In short, you gain nothing by installing the individual components yourself, and you may lose a lot. With Incredible PBX, the heavy lifting has all been done for you with documented, open source code that makes it simple to add your own tweaks as desired. That’s what open source is all about!
We’ve chosen Ubuntu 14.04 as the platform on which to begin the Incredible PBX 12 adventure. More releases will follow in due course. But Ubuntu 14.04 is an extremely stable and well-supported LTS release of Linux that warrants a careful look. After all, the primary objective here is a stable telephony platform. The Ubuntu 14.04 LTS platform offers that in spades.
Building an Ubuntu 14.04 Platform for Incredible PBX 12
As a result of the trademark and copyright morass, we’ve steered away from the bundled operating system in favor of a methodology that relies upon you to put in place the operating system platform on which to run PBX in a Flash or Incredible PBX. The good news is it’s easy! With many cloud-based providers1, you can simply click a button to choose your favorite OS flavor and within minutes, you’re ready to go. With many virtual machine platforms such as VirtualBox, it’s equally simple to find a pre-built Ubuntu 14.04 image or roll your own.
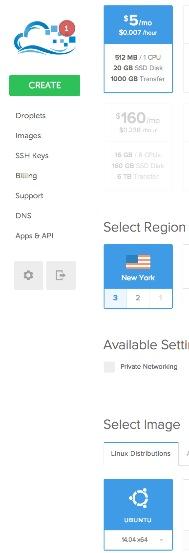 If you’re new to VoIP or to Nerd Vittles, here’s our best piece of advice. Don’t take our word for anything! Try it for yourself in the Cloud! You can build an Ubuntu 14.04 image on Digital Ocean in under one minute and install Incredible PBX 12 for Ubuntu 14.04 in under 30 minutes. Then try it out for two full months. It won’t cost you a dime. Use our referral link to sign up for an account. Enter a valid credit card to verify you’re who you say you are. Create an Ubuntu 14.04 (not 14.10!) 512MB droplet of the cheapest flavor ($5/mo.). Go to the Billing section of the site, and enter the following promo code: UBUNTUDROPLET. That’s all there is to it. A $10 credit will be added to your account, and you can play to your heart’s content. Delete droplets, add droplets, and enjoy the free ride!
If you’re new to VoIP or to Nerd Vittles, here’s our best piece of advice. Don’t take our word for anything! Try it for yourself in the Cloud! You can build an Ubuntu 14.04 image on Digital Ocean in under one minute and install Incredible PBX 12 for Ubuntu 14.04 in under 30 minutes. Then try it out for two full months. It won’t cost you a dime. Use our referral link to sign up for an account. Enter a valid credit card to verify you’re who you say you are. Create an Ubuntu 14.04 (not 14.10!) 512MB droplet of the cheapest flavor ($5/mo.). Go to the Billing section of the site, and enter the following promo code: UBUNTUDROPLET. That’s all there is to it. A $10 credit will be added to your account, and you can play to your heart’s content. Delete droplets, add droplets, and enjoy the free ride!
For today, we’ll walk you through building your own stand-alone server using the Ubuntu 14.04 mini.iso. If you’re using Digital Ocean in the Cloud, skip down to Installing Incredible PBX 12. If you’re using your own hardware, to get started, download the 32-bit or 64-bit Ubuntu 14.04 "Trusty Tahr" Minimal ISO from here. Then burn it to a CD/DVD or thumb drive and boot your dedicated server from the image. Remember, you’ll be reformatting the drive in your server so pick a machine you don’t need for other purposes.
For those that would prefer to build your Ubuntu 14.04 Wonder Machine using VirtualBox on any Windows, Mac, or existing Linux Desktop, here are the simple steps. Create a new virtual machine specifying either the 32-bit or 64-bit version of Ubuntu. Allocate 1024MB of RAM (512MB also works fine!) and at least 20GB of disk space using the default hard drive setup in all three steps. In Settings, click System and check Enable I/O APIC and uncheck Hardware Clock in UTC Time. Click Audio and Specify then Enable your sound card. Click Network and Enable Network Adapter for Adapter 1 and choose Bridged Adapter. Finally, in Storage, add the Ubuntu 14.04 mini.iso to your VirtualBox Storage Tree as shown below. Then click OK and start up your new virtual machine. Simple!
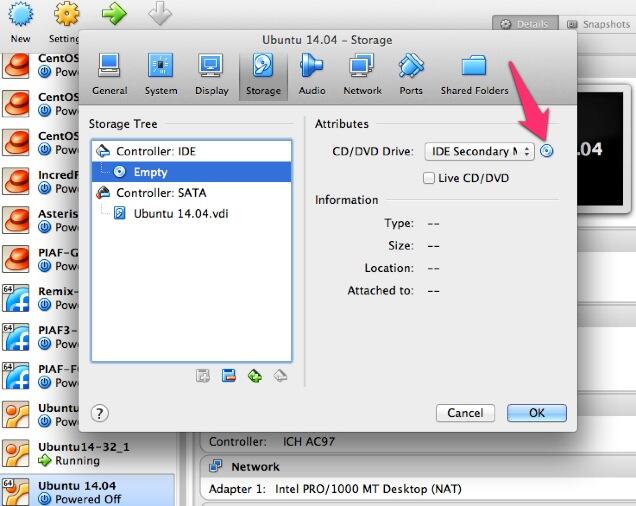
Here are the steps to get Ubuntu 14.04 humming on your new server or virtual machine once you’ve booted up. If you can bake cookies from a recipe, you can do this:
UBUNTU mini.iso install:
Choose language
Choose timezone
Detect keyboard
Hostname: incrediblepbx < continue >
Choose mirror for downloads
Confirm archive mirror
Leave proxy blank unless you need it < continue >
** couple minutes of whirring as initial components are loaded **
New user name: incredible < continue >
Account username: incredible < continue >
Account password: makeitsecure
Encrypt home directory < no >
Confirm time zone < yes >
Partition disks: Guided - use entire disk and set up LVM
Confirm disk to partition
Write changes to disks and configure LVM
Whole volume? < continue>
Write changes to disks < yes> < -- last chance to preserve your disk drive!
** about 15 minutes of whirring during base system install ** < no touchy anything>
** another 5 minutes of whirring during base software install ** < no touchy anything>
Upgrades? Install security updates automatically
** another 5 minutes of whirring during more software installs ** < no touchy anything>
Software selection: *Basic Ubuntu server (only!)
** another couple minutes of whirring during software installs ** < no touchy anything>
Grub boot loader: < yes>
UTC for system clock: < no>
Installation complete: < continue> after removing installation media
** on VirtualBox, PowerOff after reboot and remove [-] mini.iso from Storage Tree & restart VM
login as user: incredible
** enter user incredible's password **
sudo passwd
** enter incredible password again and then create secure root user password **
su root
** enter root password **
apt-get update
apt-get install ssh -y
sed -i 's|without-password|yes|' /etc/ssh/sshd_config
sed -i 's|yes"|without-password"|' /etc/ssh/sshd_config
ifconfig
** write down the IP address of your server from ifconfig results
reboot
** login via SSH to continue **
Installing Incredible PBX 12 on Your Ubuntu 14.04 Server
Adding Incredible PBX 12 to a running Ubuntu 14.04 server is a walk in the park. To restate the obvious, your server needs a reliable Internet connection to proceed. Using SSH (or Putty on a Windows machine), log into your new server as root at the IP address you deciphered in the ifconfig step at the end of the Ubuntu install procedure above.
WARNING: If you’re using a 512MB droplet at Digital Ocean, be advised that their Ubuntu setup does NOT include a swap file. This may cause serious problems when you run out of RAM. Uncomment ./create-swapfile-DO line below to create a 1GB swap file which will be activated whenever you exceed 90% RAM usage on Digital Ocean.
Now let’s begin the Incredible PBX 12 install. Log back in as root and issue the following commands:
cd /root wget http://incrediblepbx.com/incrediblepbx12.tar.gz tar zxvf incrediblepbx12.tar.gz rm incrediblepbx12.tar.gz #./create-swapfile-DO ./IncrediblePBX12.sh
The installer will first upgrade your Ubuntu 14.04 build to the latest modules. Then it will reboot. Rerun the installer again to kick off the Incredible PBX 12 installation process. Once you have agreed to the license agreement and terms of use, press Enter and go have a 30-minute cup of coffee. The Incredible PBX 12 installer runs unattended so find something to do for a bit unless you just like watching code compile. When you see "Have a nice day", your installation is complete. Write down your your three "knock" ports for PortKnocker. You can retrieve your PortKnocker setup like this: cat /root/knock.FAQ. Next, set your admin password for FreePBX 12 by running /root/admin-pw-change. Set your correct time zone by running /root/timezone-setup. To be sure your FreePBX module signatures are current, issue the following two commands:
amportal a ma refreshsignatures amportal a r
Log out and back in as root and the automatic update utility will bring your system current with security fixes and enhancements. Then you will be greeted with a status display shown at the top of this article.
You can access the Asterisk 12 CLI by typing: asterisk -rvvvvvvvvvv
You can access the FreePBX 12 GUI using your favorite web browser to configure your server. Just enter the IP address shown in the status display. The default username is admin with the admin password you set up above. If desired, you also can change it in FreePBX Administration by clicking Admin -> Administrators -> admin. Enter a new password and click Submit Changes then Apply Config. Now edit extension 701 so you can figure out (or change) the randomized passwords that were set up for default 701 extension and voicemail: Applications -> Extensions -> 701.
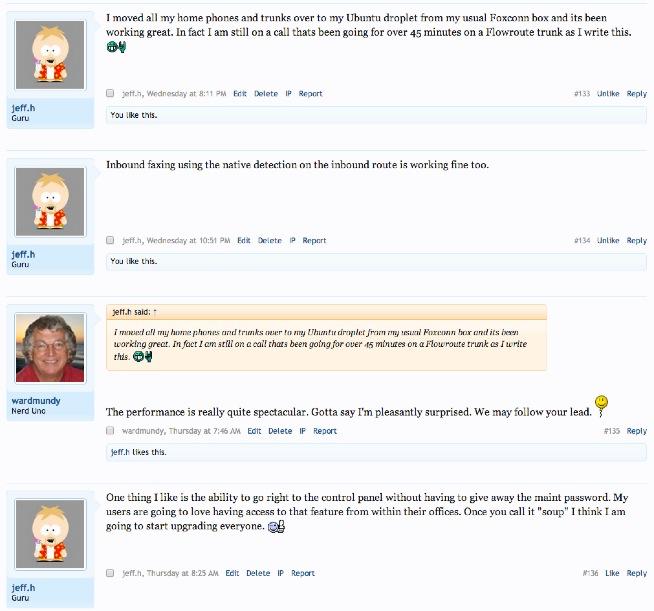
Setting Up a Soft Phone to Use with Incredible PBX
Now you’re ready to set up a telephone so that you can play with Incredible PBX 12. We recommend YateClient which is free. Download it from here. Run YateClient once you’ve installed it and enter the credentials for the 701 extension on Incredible PBX. You’ll need the IP address of your server plus your extension 701 password. Choose Settings -> Accounts and click the New button. Fill in the blanks using the IP address of your server, 701 for your account name, and whatever password you created for the extension. Click OK.
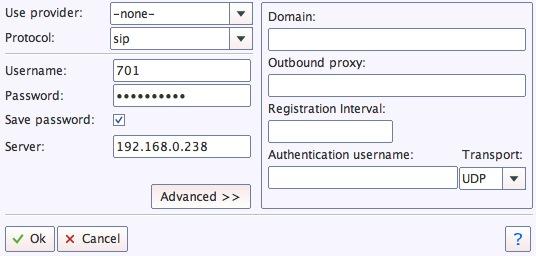
Once you are registered to extension 701, close the Account window. Then click on YATE’s Telephony Tab and place some test calls to the numerous apps that are preconfigured on Incredible PBX. Dial a few of these to get started:
123 - Reminders
222 - ODBC Demo (use acct: 12345)
947 - Weather by ZIP Code
951 - Yahoo News
*61 - Time of Day
*68 - Wakeup Call
TODAY - Today in History
Now you’re ready to connect to the telephones in the rest of the world. If you live in the U.S., the easiest way (at least for now) is to use an existing (free) Google Voice account. Google has threatened to shut this down but as this is written, it still works with previously set up Google Voice accounts. The more desirable long-term solution is to choose several SIP providers and set up redundant trunks for your incoming and outbound calls. The PIAF Forum includes dozens of recommendations to get you started.
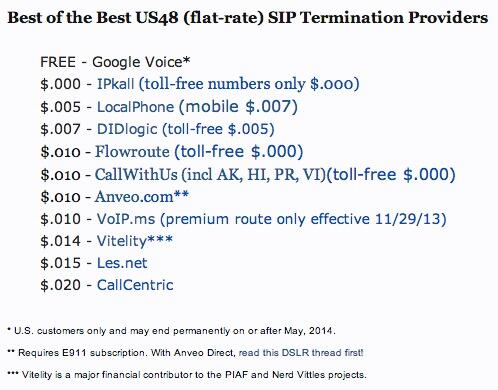
Configuring Google Voice
If you want to use Google Voice, you’ll need a dedicated Google Voice account to support Incredible PBX 12. If you want to use the inbound fax capabilities of Incredible Fax, then you’ll need an additional Google Voice line that can be routed to the FAX custom destination using FreePBX. The more obscure the username (with some embedded numbers), the better off you will be. This will keep folks from bombarding you with unsolicited Gtalk chat messages, and who knows what nefarious scheme will be discovered using Google messaging six months from now. So keep this account a secret!
We’ve tested this extensively using an existing Google Voice account, and inbound calling is just not reliable. The reason seems to be that Google always chooses Gmail chat as the inbound call destination if there are multiple registrations from the same IP address. So, be reasonable. Do it our way! Use a previously configured and dedicated Gmail and Google Voice account, and use it exclusively with Incredible PBX 12.
IMPORTANT: Be sure to enable the Google Chat option as one of your phone destinations in Settings, Voice Setting, Phones. That’s the destination we need for The Incredible PBX to work its magic! Otherwise, all inbound and outbound calls will fail. If you don’t see this option, you’re probably out of luck. Google has disabled the option in newly created accounts as well as some old ones that had Google Chat disabled. Now go back to the Google Voice Settings.
While you’re still in Google Voice Settings, click on the Calls tab. Make sure your settings match these:
- Call Screening – OFF
- Call Presentation – OFF
- Caller ID (In) – Display Caller’s Number
- Caller ID (Out) – Don’t Change Anything
- Do Not Disturb – OFF
- Call Options (Enable Recording) – OFF
- Global Spam Filtering – ON
Click Save Changes once you adjust your settings. Under the Voicemail tab, plug in your email address so you get notified of new voicemails. Down the road, receipt of a Google Voice voicemail will be a big hint that something has come unglued on your PBX.
One final word of caution is in order regardless of your choice of providers: Do NOT use special characters in any provider passwords, or nothing will work!
Now you’re ready to set up your Google Voice trunk in FreePBX 12. After logging into FreePBX with your browser, click the Connectivity tab and choose Google Voice/Motif. To Add a new Google Voice account, just fill out the form. If you want unanswered calls to be routed to Google Voice for transcription, check the box. Be advised that IVR calls typically are not "answered" so check that box as well if you plan to use an IVR to respond to incoming Google Voice calls.
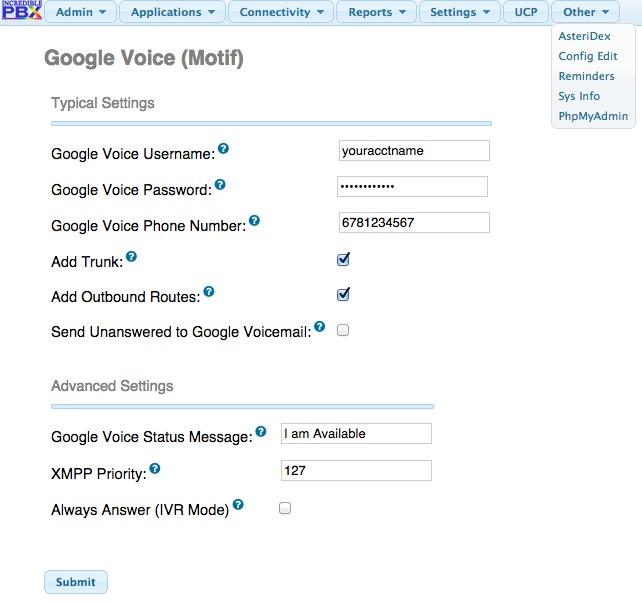
IMPORTANT LAST STEP: Google Voice will not work unless you restart Asterisk from the Linux command line at this juncture. Using SSH, log into your server as root and issue the following command: amportal restart.
If you have trouble getting Google Voice to work (especially if you have previously used your Google Voice account from a different IP address), try this Google Voice Reset Procedure. It usually fixes connectivity problems. If it still doesn’t work, enable Less Secure Apps using this Google tool.
Troubleshooting Audio and DTMF Problems
You can avoid one-way audio on calls and touchtones that don’t work with these simple settings in FreePBX: Settings -> Asterisk SIP Settings. Just plug in your public IP address and your private IP subnet. Then set ULAW as the only Audio Codec.
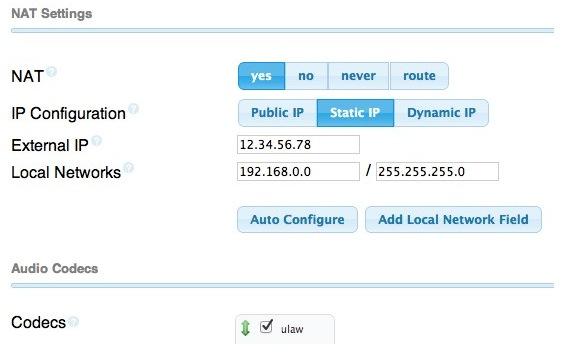
Adding Speech Recognition to Incredible PBX 12
To support many of our applications, Incredible PBX has included Google’s speech recognition service for years. These applications include Weather Reports by City (949), AsteriDex Voice Dialing by Name (411), and Wolfram Alpha for Asterisk (4747), all of which use Lefteris Zafiris’ terrific speech-recog AGI script. Unfortunately (for some), Google now has tightened up the terms of use for their free speech recognition service. Now you can only use it for "personal and development use." If you meet those criteria, keep reading. Here’s how to activate speech recognition on Incredible PBX. Don’t skip any steps!
1. Using an existing Google/Gmail account to join the Chrome-Dev Group.
2. Using the same account, create a new Speech Recognition Project.
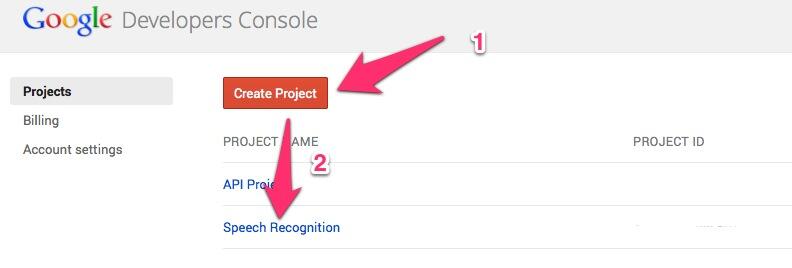
3. Click on your newly created project and choose APIs & auth.
4. Turn ON Speech API by clicking on its Status button in the far right margin.
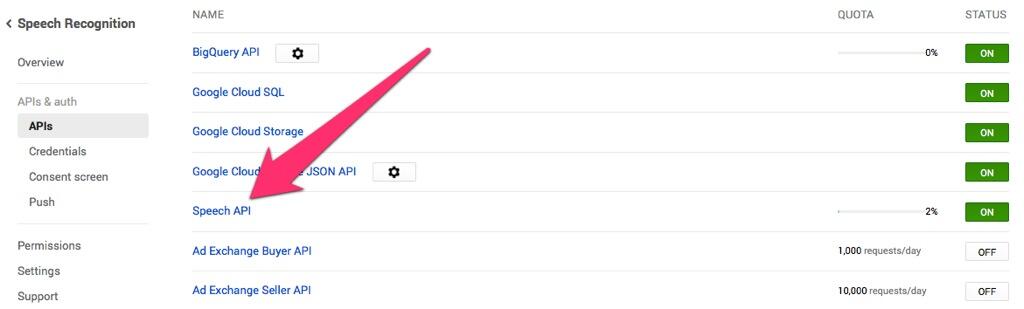
5. Click on Credentials in APIs & auth and choose Create New Key -> Server key. Leave the IP address restriction blank!
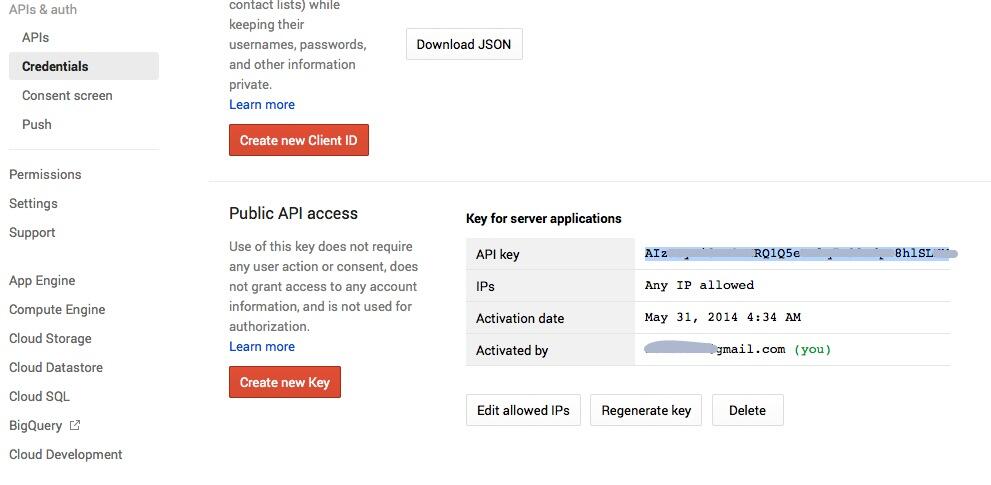
6. Write down your new API key or copy it to the clipboard.
7. Log into your server as root and issue the following commands:
# for Ubuntu and Debian platforms apt-get clean apt-get install libjson-perl flac -y # for RedHat and CentOS platforms # yum -y install perl-JSON # for all Linux platforms cd /var/lib/asterisk/agi-bin mv speech-recog.agi speech-recog.last.agi wget --no-check-certificate https://raw.githubusercontent.com/zaf/asterisk-speech-recog/master/speech-recog.agi chown asterisk:asterisk speech* chmod 775 speech* nano -w speech-recog.agi
8. When the nano editor opens, go to line 70 of speech-recog.agi: my $key = "". Insert your API key from Step #6 above between the quotation marks and save the file: Ctrl-X, Y, then Enter.
Now you’re ready to try out the speech recognition apps. Dial 949 and say the name of a city and state/province/country to get a current weather forecast from Yahoo. Dial 411 and say "American Airlines" to be connected to American.
To use Wolfram Alpha by phone, you first must install it. Obtain your free Wolfram Alpha APP-ID here. Then run the one-click installer: /root/wolfram/wolframalpha-oneclick.sh. Insert your APP-ID when prompted. Now dial 4747 to access Wolfram Alpha by phone and enter your query, e.g. "What planes are overhead." Read the Nerd Vittles tutorial for additional examples and tips.
A Few Words about the Incredible PBX 12 Security Model for Ubuntu
Incredible PBX 12 for Ubuntu 14.04 is an extremely secure turnkey PBX implementation. As configured, it is protected by both Fail2Ban and a hardened configuration of the IPtables Linux firewall. As installed, nobody can access your PBX without  your credentials AND
your credentials AND  an IP address that is either on your private network or that matches the IP address of your server or the PC from which you installed Incredible PBX. Incredible PBX 12 is preconfigured to let you connect to many of the leading SIP hosting providers without additional firewall tweaking.
an IP address that is either on your private network or that matches the IP address of your server or the PC from which you installed Incredible PBX. Incredible PBX 12 is preconfigured to let you connect to many of the leading SIP hosting providers without additional firewall tweaking.
You can whitelist additional IP addresses for remote access in several ways. First, you can use the command-line utilities: /root/add-ip and /root/add-fqdn. You can also remove whitelisted IP addresses by running /root/del-acct. Second, you can dial into extension 864 (or use a DID pointed to extension 864 aka TM4) and enter an IP address to whitelist. Before Travelin’ Man 4 will work, you’ll need to add credentials for each caller using the tools in /root/tm4. You must add at least one account before dial-in whitelisting will be enabled. Third, you can temporarily whitelist an IP address by successfully executing the PortKnocker 3-knock code established for your server. You’ll find the details and the codes in /root/knock.FAQ. Be advised that IP addresses whitelisted with PortKnocker (only!) go away whenever your server is rebooted or the IPtables firewall is restarted. For further information on the PortKnocker technology and available clients for iOS and Android devices, review the Nerd Vittles tutorial.
HINT: The reason that storing your PortKnocker codes in a safe place is essential is because it may be your only available way to gain access to your server if your IP address changes. You obviously can’t use the command-line tools to whitelist a new IP address if you cannot gain access to your server at the new IP address.
We always recommend you also add an extra layer of protection by running your server behind a hardware-based firewall with no Internet port exposure, but that’s your call. If you use a hardware-based firewall, be sure to map the three PortKnocker ports to the internal IP address of your server!
The NeoRouter VPN client also is included for rock-solid, secure connectivity for remote users. Read our previous tutorial for setup instructions.
As one would expect, the IPtables firewall is a complex piece of software. If you need assistance configuring it, visit the PIAF Forum for some friendly assistance.
Incredible Backup and Restore
We’re pleased to introduce our latest backup and restore utilities for Incredible PBX. Running /root/incrediblebackup will create a backup image of your server in /tmp. This backup image then can be copied to any other medium desired for storage. To restore it to another Incredible PBX 12 server, simply copy the image to a server running Asterisk 12 and FreePBX 12 and run /root/incrediblerestore. Doesn’t get much simpler than that.
A Word About FreePBX Module Signatures
FreePBX 12 has implemented a new checksum mechanism to assure that modules are intact. Special thanks to the FreePBX Development Team for their work in extending this feature to modules outside the FreePBX-support modules. If other modules (other than ODBC configuration files) show invalid or missing signatures, you should do some investigating promptly!
Adding Incredible Fax to Your Server
Once you’ve completed the Incredible PBX install, log out and log back in to load the latest automatic updates. Then reboot. Now you’re ready to continue your adventure by installing Incredible Fax for Ubuntu. Special thanks to Josh North for all his hard work on this!
cd /root rm incrediblefax11_ubuntu14.sh wget http://incrediblepbx.com/incrediblefax11_ubuntu14.sh chmod +x incrediblefax11_ubuntu14.sh ./incrediblefax11_ubuntu14.sh
Just plug in your email address for delivery of your incoming faxes in PDF format. Then accept all of the defaults during the installation process. Once you complete the install, reboot your server. Then log in as root again and set your AvantFax admin password: /root/avantfax-pw-change. Now you can access both FreePBX 12 and AvantFax by pointing your browser to the IP address of your server. Please note that we’ve had problems logging into AvantFax with some versions of the Chrome browser. Works great with Firefox!
Next, log into FreePBX and set an Inbound Route for incoming faxes to Custom Destination: Fax (hylafax). Then try sending a fax to the phone number and be sure it arrives in your email.
You also can try enabling fax detection with any Google Voice number. Just edit the inbound route for the DID and make it look like this:

Incredible PBX 12 Automatic Update Utility
Every time you log into your server as root, Incredible PBX 12 will ping the IncrediblePBX.com web site to determine whether one or more updates are available to bring your server up to current specs. We recommend you log in at least once a week just in case some new security vulnerability should come along (again).
Where To Go Next?
Once you get Incredible PBX installed, you’ll want to read up on the dozens of applications for Asterisk which are included in the Incredible PBX feature set. We’ve previously covered this in a separate article for the Raspberry Pi platform, but the applications are the same. Here’s a link to the tutorials.
You can follow updates to Incredible PBX 12 in this thread on the PIAF Forum.
We would also encourage you to sign up for an account on the PIAF Forum and join the discussion. In addition to providing first-class, free support, we think you’ll enjoy the camaraderie. Come join us!
Originally published: Monday, November 3, 2014 Updated: Monday, December 1, 2014
 Support Issues. With any application as sophisticated as this one, you’re bound to have questions. Blog comments are a terrible place to handle support issues although we welcome general comments about our articles and software. If you have particular support issues, we encourage you to get actively involved in the PBX in a Flash Forums. It’s the best Asterisk tech support site in the business, and it’s all free! Please have a look and post your support questions there. Unlike some forums, ours is extremely friendly and is supported by literally hundreds of Asterisk gurus and thousands of users just like you. You won’t have to wait long for an answer to your question.
Support Issues. With any application as sophisticated as this one, you’re bound to have questions. Blog comments are a terrible place to handle support issues although we welcome general comments about our articles and software. If you have particular support issues, we encourage you to get actively involved in the PBX in a Flash Forums. It’s the best Asterisk tech support site in the business, and it’s all free! Please have a look and post your support questions there. Unlike some forums, ours is extremely friendly and is supported by literally hundreds of Asterisk gurus and thousands of users just like you. You won’t have to wait long for an answer to your question.

Need help with Asterisk? Visit the PBX in a Flash Forum.
Special Thanks to Our Generous Sponsors
FULL DISCLOSURE: ClearlyIP, Skyetel, Vitelity, DigitalOcean, Vultr, VoIP.ms, 3CX, Sangoma, TelecomsXchange and VitalPBX have provided financial support to Nerd Vittles and our open source projects through advertising, referral revenue, and/or merchandise. As an Amazon Associate and Best Buy Affiliate, we also earn from qualifying purchases. We’ve chosen these providers not the other way around. Our decisions are based upon their corporate reputation and the quality of their offerings and pricing. Our recommendations regarding technology are reached without regard to financial compensation except in situations in which comparable products at comparable pricing are available from multiple sources. In this limited case, we support our sponsors because our sponsors support us.
 BOGO Bonaza: Enjoy state-of-the-art VoIP service with a $10 credit and half-price SIP service on up to $500 of Skyetel trunking with free number porting when you fund your Skyetel account. No limits on number of simultaneous calls. Quadruple data center redundancy. $25 monthly minimum spend required. Tutorial and sign up details are here.
BOGO Bonaza: Enjoy state-of-the-art VoIP service with a $10 credit and half-price SIP service on up to $500 of Skyetel trunking with free number porting when you fund your Skyetel account. No limits on number of simultaneous calls. Quadruple data center redundancy. $25 monthly minimum spend required. Tutorial and sign up details are here.
 The lynchpin of Incredible PBX 2020 and beyond is ClearlyIP components which bring management of FreePBX modules and SIP phone integration to a level never before available with any other Asterisk distribution. And now you can configure and reconfigure your new Incredible PBX phones from the convenience of the Incredible PBX GUI.
The lynchpin of Incredible PBX 2020 and beyond is ClearlyIP components which bring management of FreePBX modules and SIP phone integration to a level never before available with any other Asterisk distribution. And now you can configure and reconfigure your new Incredible PBX phones from the convenience of the Incredible PBX GUI.
 VitalPBX is perhaps the fastest-growing PBX offering based upon Asterisk with an installed presence in more than 100 countries worldwide. VitalPBX has generously provided a customized White Label version of Incredible PBX tailored for use with all Incredible PBX and VitalPBX custom applications. Follow this link for a free test drive!
VitalPBX is perhaps the fastest-growing PBX offering based upon Asterisk with an installed presence in more than 100 countries worldwide. VitalPBX has generously provided a customized White Label version of Incredible PBX tailored for use with all Incredible PBX and VitalPBX custom applications. Follow this link for a free test drive!
 Special Thanks to Vitelity. Vitelity is now Voyant Communications and has halted new registrations for the time being. Our special thanks to Vitelity for their unwavering financial support over many years and to the many Nerd Vittles readers who continue to enjoy the benefits of their service offerings. We will keep everyone posted on further developments.
Special Thanks to Vitelity. Vitelity is now Voyant Communications and has halted new registrations for the time being. Our special thanks to Vitelity for their unwavering financial support over many years and to the many Nerd Vittles readers who continue to enjoy the benefits of their service offerings. We will keep everyone posted on further developments.
Some Recent Nerd Vittles Articles of Interest…
- With some providers including ones linked in this article, Nerd Vittles receives referral fees which assist in keeping the Nerd Vittles lights burning brightly. [↩]
A Firsthand Look at Disaster Recovery: Tethering and IAX with Asterisk

One of the exciting challenges of building a swimming pool is knowing that it’s just a matter of time until your Internet connection dies. As you might imagine, swimming pools are major construction and involve a lot of digging. And digging usually means some oops moments when cables get cut. In our case, we had watched the folks digging the trenches for all of the pool plumbing to be sure they didn’t accidentally whack one of three coax cables coming into our house. And, when it came time to cover up the trenches, we pointed out the orange cables to the Bobcat driver knowing we were finally home free. Not so fast! Two minutes later, Mario had driven the Bobcat right over the primary Internet cable leaving the shredded remains sticking up through the dirt. Oops. Sorry. Shit happens!
Looking on the positive side, we chuckled, "What a perfect opportunity to test our backup Asterisk® system!" Our backup system is pretty clever if we do say so. It relies upon a Verizon WiFi HotSpot running on our Galaxy smartphone and a duplicate of our Asterisk-based PBX in a Flash™ server running as a virtual machine under VirtualBox on an iMac desktop. The entire setup takes less than a minute to activate. Well, that was the plan anyway.
It turns out that Verizon does SIP a little differently with a SIP ALG in the path so Asterisk couldn’t register with all but one of our dozen SIP providers. Congratulations, CallCentric! The workaround is to enable STUN. That is now possible with Asterisk 11. Short of that, you’re left with CallCentric. Unfortunately for us, we don’t do much SIP trunking with CallCentric, and none of our primary DIDs are connected through them. The other option is to add port=5080 to your trunk setup with any SIP trunks you register with VoIP.ms using a username and password. Our attention span was too short to tackle STUN in the middle of this crisis. But there’s good news. Verizon doesn’t mess with IAX network traffic at all. Since a couple of our primary DIDs are registered with VoIP.ms using IAX trunks, restoring these IAX trunks to full functionality took less than a minute. That is step one of a three-step process. You need inbound trunks, phones, and outbound trunks to get your redundant VoIP server back in business.

Getting phones to function on what is now a purely WiFi network (through the Verizon HotSpot) can be problematic unless you’ve done your homework and sprinkled a few WiFi-capable SIP phones around your home or office. In our case, we still have Grandstream’s GXP2200 Android phones scattered everywhere so it was just a matter of plugging in the WiFI adapters and rebooting. The newer GXV3240 would work just as well.1
All that remained was enabling several trunks for outbound calls. Since VoIP.ms IAX trunks support both incoming and outgoing calls, we were home free. And, with Google Voice trunks, it was simply a matter of jumping through Google’s security hoops to reenable the connections on a new IP address.
Lessons Learned. Here’s a quick checklist for those of you that think about disaster recovery for your home or for clients and businesses. Nothing beats some advance planning. If money is no object, then WiFi tethering from a smartphone with one of the major providers whose service works well in your home or office environment is the way to go. 4G is a must!
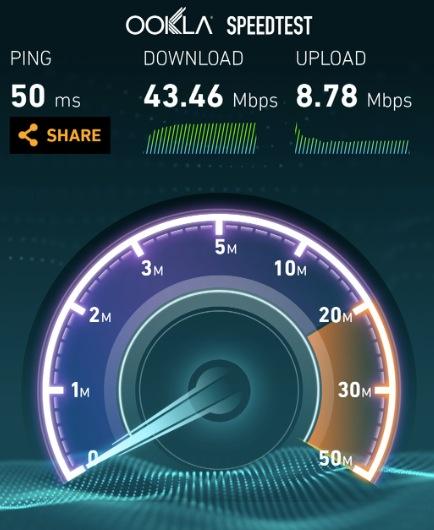
In our case, money was an object so we had the foresight to acquire a Verizon SIM card from eBay that included an unlimited data plan. With this setup, it costs only $1 a day extra to add WiFi tethering, and you can turn it off and on as often as you like without any additional fees or surcharges. There also are no additional charges for using boatloads of data! We’re actually writing this column with a tethered connection from a hotel in Washington (results above). To give you some idea of why an unlimited data plan is important, our home operation burned through 4 gigs of data in less than 24 hours once we activated WiFi tethering. Of course, there were people doing things other than making phones calls, but tethering enables 5 connections to function just about like the cable modem service you originally had in place. So expect the data usage to be substantial. Everybody likes 24/7 Internet service.
Loss of phone calls through a PBX is more of an annoyance than a crisis these days because almost everyone also has a smartphone. Even so, the SIP gotcha with Verizon Wireless was a surprise because we hadn’t really tested our super-duper emergency system in advance. That wasn’t too smart obviously. The old adage applies. Do as we say, not as we do. Unplug your cable modem or DSL connection and actually test your backup system before D-Day arrives.
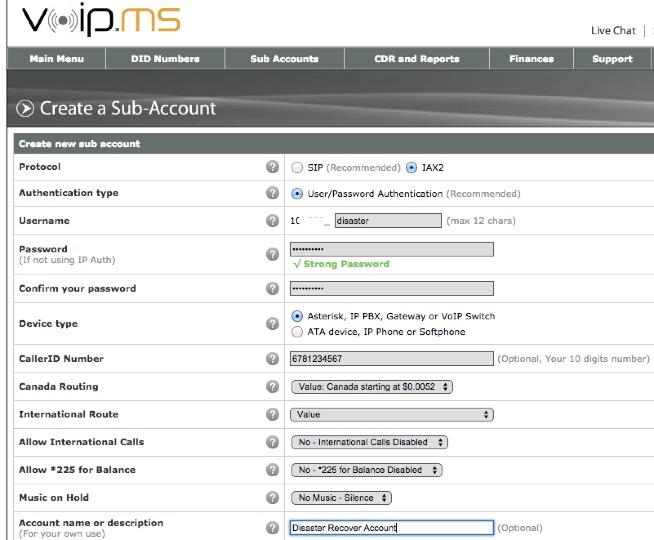
On the VoIP provider end, now is the time to set up an account with a provider that offers both SIP and IAX connectivity. Step 2 is to actually configure an IAX trunk (as a subaccount to use VoIP.ms parlance) and test it. IAX trunks actually have fewer headaches with NAT, but there are only a handful of providers that still provide the service. Find one now and make certain that your primary DIDs will roll over to the IAX trunk in case of an outage. I’m always reminded that we have Mark Spencer to thank for IAX. It was his brainchild. Thank you, Mark! With VoIP.ms, you also can spoof your CallerID so that calls will still appear to originate from your primary Asterisk PBX.
Keep in mind that a VirtualBox-based Asterisk virtual machine and a Desktop computer both need an IP address and will have to be started on WLAN0 rather than ETH0. Remember, your wired connection is now dead.
You’re also going to want to acquire at least a couple of WiFi-capable SIP phones that can be connected with your Asterisk server using your WiFi HotSpot. Also make certain that you have a preconfigured IPtables firewall on your backup system. Remember, your hardware-based firewall connected to your cable modem won’t provide any protection once you switch to HotSpot operation. Lucky for you, Incredible PBX™ servers come preconfigured with a locked-down IPtables firewall and a WhiteList. Just add the new IP addresses of your server and phones, and you’re secure on the public Internet.
Finally, let’s do the HotSpot connection math. You’ll need an IP address for your desktop computer running VirtualBox. You’ll need a second IP address for the Asterisk virtual machine. Then you’ll need an IP address for every WiFi-enabled SIP phone. If the maximum number of connections is five on your HotSpot, that means you’ve got the necessary capacity for at most 3 WiFi SIP phones assuming you don’t enable a WiFi printer and if nobody else wants to use a computer during the outage. The other option is to add an inexpensive travel router with bridge mode to your mix of 5 devices. We always keep one handy for extended trips. A properly configured travel router provides an additional WiFi network with some extra WiFi connections. Good luck!
Security Alerts. Serious SSL and FreePBX security vulnerabilities have been discovered AND patched during the past week. If you have not patched your server and Asterisk, FreePBX, Apache, and/or WebMin are exposed to the public Internet, you have a serious problem on your hands. See this thread for details on the FreePBX vulnerability. And see this thread for the steps necessary to patch SSL in Asterisk, Apache, and Webmin. While Incredible PBX servers were automatically patched for the FreePBX vulnerability, the SSL issues require manual patching and an Asterisk upgrade. A script for upgrading Asterisk 11 servers is included in the message thread linked above. ALWAYS run your VoIP server behind a firewall with no Internet port exposure to Asterisk, FreePBX, SSH, or the Apache and Webmin web servers! And, if you think all of this security stuff is just a silly waste of your time, then read about the latest lucky recipient of a $166,000 phone bill.
Originally published: Monday, October 20, 2014

Need help with Asterisk? Visit the PBX in a Flash Forum.
Special Thanks to Our Generous Sponsors
FULL DISCLOSURE: ClearlyIP, Skyetel, Vitelity, DigitalOcean, Vultr, VoIP.ms, 3CX, Sangoma, TelecomsXchange and VitalPBX have provided financial support to Nerd Vittles and our open source projects through advertising, referral revenue, and/or merchandise. As an Amazon Associate and Best Buy Affiliate, we also earn from qualifying purchases. We’ve chosen these providers not the other way around. Our decisions are based upon their corporate reputation and the quality of their offerings and pricing. Our recommendations regarding technology are reached without regard to financial compensation except in situations in which comparable products at comparable pricing are available from multiple sources. In this limited case, we support our sponsors because our sponsors support us.
 BOGO Bonaza: Enjoy state-of-the-art VoIP service with a $10 credit and half-price SIP service on up to $500 of Skyetel trunking with free number porting when you fund your Skyetel account. No limits on number of simultaneous calls. Quadruple data center redundancy. $25 monthly minimum spend required. Tutorial and sign up details are here.
BOGO Bonaza: Enjoy state-of-the-art VoIP service with a $10 credit and half-price SIP service on up to $500 of Skyetel trunking with free number porting when you fund your Skyetel account. No limits on number of simultaneous calls. Quadruple data center redundancy. $25 monthly minimum spend required. Tutorial and sign up details are here.
 The lynchpin of Incredible PBX 2020 and beyond is ClearlyIP components which bring management of FreePBX modules and SIP phone integration to a level never before available with any other Asterisk distribution. And now you can configure and reconfigure your new Incredible PBX phones from the convenience of the Incredible PBX GUI.
The lynchpin of Incredible PBX 2020 and beyond is ClearlyIP components which bring management of FreePBX modules and SIP phone integration to a level never before available with any other Asterisk distribution. And now you can configure and reconfigure your new Incredible PBX phones from the convenience of the Incredible PBX GUI.
 VitalPBX is perhaps the fastest-growing PBX offering based upon Asterisk with an installed presence in more than 100 countries worldwide. VitalPBX has generously provided a customized White Label version of Incredible PBX tailored for use with all Incredible PBX and VitalPBX custom applications. Follow this link for a free test drive!
VitalPBX is perhaps the fastest-growing PBX offering based upon Asterisk with an installed presence in more than 100 countries worldwide. VitalPBX has generously provided a customized White Label version of Incredible PBX tailored for use with all Incredible PBX and VitalPBX custom applications. Follow this link for a free test drive!
 Special Thanks to Vitelity. Vitelity is now Voyant Communications and has halted new registrations for the time being. Our special thanks to Vitelity for their unwavering financial support over many years and to the many Nerd Vittles readers who continue to enjoy the benefits of their service offerings. We will keep everyone posted on further developments.
Special Thanks to Vitelity. Vitelity is now Voyant Communications and has halted new registrations for the time being. Our special thanks to Vitelity for their unwavering financial support over many years and to the many Nerd Vittles readers who continue to enjoy the benefits of their service offerings. We will keep everyone posted on further developments.
Some Recent Nerd Vittles Articles of Interest…
- Some of our links refer users to Amazon or other service providers when we find their prices are competitive for the recommended products. Nerd Vittles receives a small referral fee from these providers to help cover the costs of our blog. We never recommend particular products solely to generate commissions. However, when pricing is comparable or availability is favorable, we support these providers because they support us. [↩]
Zero Day Vulnerability Protection and More: Introducing Cover Your Asterisk
It’s been a difficult couple of weeks for the Linux® and Asterisk® communities with the back-to-back disclosures of the BASH Shellshock bug and then the FreePBX® Asterisk Recording Interface (ARI) bug a few days later. Both of these vulnerabilities have been circulating in the wild for years. We won’t repeat Wikipedia’s Zero Day Attack analysis other than to note that what makes these particular bugs so scary is not only the fact that both went undetected and unpatched for years but also that the attack vectors for both bugs were so simple. Anyone with a web server exposed to the Internet that was running any flavor of Linux or any Asterisk server with the FreePBX GUI was fair game for a seriously compromised server.
For those with shared servers in a hosted environment running under cPanel, your web platform typically runs with the equivalent of root privileges which means that any web intrusion inherits the same server privileges that you as the administrator had. This is similar to the way FreePBX runs with Asterisk. The same user account used for web access controls all of the Asterisk assets on your server. While it’s convenient, it’s also dangerous whenever there’s a web vulnerability because the entire Asterisk platform has exposure.
We always chuckle when one of the anonymous forum trolls launches a tirade claiming that these alerts are nothing more than Monday morning quarterbacking disguised as Chicken Little. What’s more amazing is that anyone would take the comments of an anonymous poster seriously especially on a matter involving server security. It’s one thing to label folks as alarmists for suggesting that the sky is falling when it isn’t. It’s quite another to launch these anonymous personal attacks even when there is documented evidence that the Internet sky was indeed caving in. Kinda reminds us of the global warming naysayers when the polar ice caps are melting beneath their feet.
According to the naysayers, we’re all doomed when it comes to cyberterrorism so why fight it. Here’s why. While reacting to security vulnerabilities has always been a defensive game of cat and mouse, that doesn’t mean you shouldn’t proactively do what you can to patch serious security holes in your servers. The alternative is to give cybercriminals a blank check to launch bots from your server that generate spam or participate in large-scale zombie attacks on our most trusted resources whether they’re DNS root servers, utility infrastructure and our electric grid, banking assets, and even national security resources. So let’s circle back and address what you can do to assure that you’re part of the solution rather than part of the problem.
The Way It Is: Do I Need a Public Web Server with Asterisk?
For purposes of this discussion, our focus today is Asterisk server security. And the number one thing you can do to insulate your server from these vulnerabilities is to make certain that your web server is not exposed to Internet access by the general public. Neither Asterisk nor FreePBX requires public web server access to manage your server. In fact, neither Asterisk nor FreePBX requires any public access to your server to properly perform all required telecommunications functions. And the second paragraph above explains why this is especially dangerous with servers running both Asterisk and FreePBX.
So why do people still publicly expose their web servers and UDP ports 5060 and 10000-20000 to the Internet? As much as we hate to say it, it’s because it’s always been done that way. It’s also because there are a handful of SIP providers that still require UDP 5060 access to make and receive calls. Most do not! And even for those that do require UDP 5060 access, their requirements can be satisfied with a properly configured firewall that supports whitelisting of "safe" IP addresses for limited access. Incredible PBX comes preconfigured with a locked down WhiteList. The same can be added to PBX in a Flash by installing Travelin’ Man 3. We hope the other aggregations will follow suit. It’s long overdue.
Public web server access often is because there are more than a few (lazy) VoIP providers that install systems in a way that makes it easy for them to manage remote sites. Of course, a VPN would provide secure access to the same resources but that’s a little more work on the deployment end. With NeoRouter VPN, it’s a 5-minute job!
There also are companies with remote users or traveling salesmen that claim their servers must be open to the Internet to keep the company running. First, it’s hard to imagine a company whose salespeople don’t have cellphones that require no link to home base. Second, there are numerous solutions for safe connectivity with a home office: VPNs, FQDNs with dynamic DNS support, Port Knocker, and Travelin’ Man 4 to name just a few of the ones we previously have recommended. With the exception of the lazy VoIP installer, you will note that none of the above scenarios ever require web access to a VoIP server. So the rationale for public exposure of an Asterisk web server is all but non-existent.
The bottom line is that, if your server is not and has never been accessible from the Internet by typing its IP address into a public web browser and assuming your root password has not been compromised, then the BASH and ARI vulnerabilities are purely an academic discussion from your vantage point. Should you apply the patches anyway? Absolutely. Will your server be compromised if you don’t? Probably not… at least not from these two vulnerabilities.
Life Is Good: Why Do I Need ‘Cover Your Asterisk’
That brings us to our topic for today. Having said all of the above, how do you really know if your server has been compromised by some zero day attack vector that none of us yet know about? After all, there are tens of thousands of applications installed on a typical Linux server. And a zero day vulnerability could be hiding almost anywhere.
First, a few words about what Cover Your Asterisk is not. This application won’t detect previously compromised servers! Wearing a condom the day after your wild night on the town isn’t all that helpful. If your server has been running as a public web server for the last 5 years, then our best advice is to start with a fresh install to a new, secured server. Then manually copy the settings (not the files!) from your old server to the new platform. Now you’re ready to protect your server.
Second, more than a few words about the VoIP environment in which we find ourselves. If you’re running any of the so-called Asterisk aggregations including PBX in a Flash, Incredible PBX, AsteriskNOW, FreePBX Distro, or Elastix, then your server includes some flavor of the FreePBX GUI, a web-based application to manage and configure Asterisk. As part of the FreePBX GUI setup, you give FreePBX 2.11 and beyond an expansive set of privileges on your server. These include read, write, and delete access to all of your web assets, all of your VoIP-related MySQL database assets, and all of your Asterisk assets. You also grant FreePBX rights to inventory and monitor critical pieces of information about your server so that you can be informed about pertinent FreePBX updates. We don’t see this as a bad thing. But, even with the incredibly talented FreePBX development team, this application design can be dangerous for a number of reasons not the least of which is the events of the past week. Consider for a moment a scenario in which a disgruntled employee or a web vulnerability allows somebody to modify a critical Asterisk configuration file such as manager.conf which controls access to the Asterisk Manager Interface, or to adjust MySQL’s admin.ampusers table which controls web access to the FreePBX GUI, or even to insert a malicious module into FreePBX which "looks and feels" like part of FreePBX. When you don’t know what you’re looking for, detecting subtle changes can be extremely difficult even for the most talented people in the business. For everyone else, it’s next to impossible. This is especially true when the changes aren’t noticeable in the standard day-to-day operation of your server. That was what led us to conclude that an additional detection mechanism was essential to highlight hidden changes made to any of the critical components that make up the Asterisk platform. Thus was born Cover Your Asterisk.
The Elastix folks apparently weren’t comfortable with this arrangement and forked FreePBX years ago and moved to a self-managed environment. The drawback has been their pace of releasing updates and patches, and that apparently applies to the unaddressed ARI bug as well.
The remaining aggregations all function as we’ve described. Before we delve into Cover Your Asterisk, here’s a little known tip. On the output side, FreePBX is basically a code-generator for Asterisk. Once you’ve configured your server using the FreePBX GUI, there is no Asterisk-FreePBX linkage of which we’re aware that requires your web server to remain operational. That turns out to be a good thing. What this means is you can shut down Apache and still have a fully functional Asterisk server with all of the functionality of your FreePBX-designed configuration. Given the times in which we live, that may not be such a bad idea.
An Overview of Cover Your Asterisk
So what does Cover Your Asterisk do? What we’ve sought to do with this GPL2 application is to take a snapshot of your most valuable Asterisk and FreePBX assets and then create checksums of all the individual components. This includes the /etc/asterisk, /var/www/html/admin, and /var/lib/asterisk/agi-bin directories as well as the Asterisk DB and MySQL’s asterisk database. Periodically, you then run another script which compares your current setup to the previous snapshot and identifies the changes for further examination. Once you are satisfied that any reported changes are legitimate, you then take a new snapshot of your server and periodically check it to make certain no unexpected modifications have crept into your system. A duplicate of these production assets is always maintained in a separate directory structure (/etc/asterisk.snapshot) accessible only by root. It can easily be converted into a gzipped tarball: tar -cvzf cya.tar.gz /etc/asterisk.snapshot. Then simply store the tarball off site for a rainy day emergency… when the sky falls once again.
Because this application was designed for production servers, its testing and scope have been limited to the Asterisk 11 and FreePBX 2.11 platform. For our installed base, that translates into PIAF-Green with FreePBX 2.11 and all flavors of Incredible PBX 11 running atop CentOS, Scientific Linux, Ubuntu 14, Debian, and Raspbian platforms on both Intel and ARM hardware including the Raspberry Pi, BeagleBone Black, CuBox, and PogoPlug.
Installation and Operation of Cover Your Asterisk
Log into your Asterisk 11 server as root and issue the following commands to install the Cover Your Asterisk software:
cd /root wget http://incrediblepbx.com/cover-your-Asterisk.tar.gz tar zxvf cover-your-Asterisk.tar.gz rm -f cover-your-Asterisk.tar.gz
To take the original snapshot of your server, run: /root/protect-your-ASSets.sh
To check your current setup against the snapshot, run: /root/check-your-ASSets.sh
To compare a file with its snapshot, run: diff /dirpath/filename /etc/asterisk.snapshot/dirpath/filename
To restore a snapshot file to your current Asterisk configuration, run these commands:
cp -p /etc/asterisk.snapshot/etc/asterisk/filename /etc/asterisk/filename amportal restart
For Raspberry Pi and BeagleBone Black users, change the MySQL root password in both scripts:
sed -i 's|passw0rd|raspberry|' /root/protect-your-ASSets.sh sed -i 's|passw0rd|raspberry|' /root/check-your-ASSets.sh
Finally, let us close with several recommendations. First, before making changes to your server with FreePBX, always run check-your-ASSets.sh, correct any detected problems, and then run protect-your-ASSets.sh to create a new snapshot of your server. After making any changes with the FreePBX GUI, run check-your-ASSets.sh again to verify that the changes you sought to make were, in fact, the changes that actually were made to your server. Then finish up by taking a new snapshot. These scripts take less than 30 seconds to run on a typical server so this is not a cumbersome process.
Before you restore any snapshot file or if you are puzzled by any changes you see listed after running check-your-ASSets.sh, we strongly recommend that you first seek advice from the gurus on the PIAF Forum. They can help you identify the severity of the problem, if any, and recommend an appropriate course of action for correction of the problem.
Finally, a cautionary note. Cover Your Asterisk is still a project in development. This means there will be changes/improvements as the coming weeks go by. One wrinkle with updates is your previous snapshots will have to be checked before you update. And then the newest protect-your-ASSets.sh script will need to be run following the update. To keep track of future releases and what’s included, visit this development thread on the PIAF Forum. Enjoy!
Originally published: Monday, October 6, 2014

Need help with Asterisk? Visit the PBX in a Flash Forum.
Special Thanks to Our Generous Sponsors
FULL DISCLOSURE: ClearlyIP, Skyetel, Vitelity, DigitalOcean, Vultr, VoIP.ms, 3CX, Sangoma, TelecomsXchange and VitalPBX have provided financial support to Nerd Vittles and our open source projects through advertising, referral revenue, and/or merchandise. As an Amazon Associate and Best Buy Affiliate, we also earn from qualifying purchases. We’ve chosen these providers not the other way around. Our decisions are based upon their corporate reputation and the quality of their offerings and pricing. Our recommendations regarding technology are reached without regard to financial compensation except in situations in which comparable products at comparable pricing are available from multiple sources. In this limited case, we support our sponsors because our sponsors support us.
 BOGO Bonaza: Enjoy state-of-the-art VoIP service with a $10 credit and half-price SIP service on up to $500 of Skyetel trunking with free number porting when you fund your Skyetel account. No limits on number of simultaneous calls. Quadruple data center redundancy. $25 monthly minimum spend required. Tutorial and sign up details are here.
BOGO Bonaza: Enjoy state-of-the-art VoIP service with a $10 credit and half-price SIP service on up to $500 of Skyetel trunking with free number porting when you fund your Skyetel account. No limits on number of simultaneous calls. Quadruple data center redundancy. $25 monthly minimum spend required. Tutorial and sign up details are here.
 The lynchpin of Incredible PBX 2020 and beyond is ClearlyIP components which bring management of FreePBX modules and SIP phone integration to a level never before available with any other Asterisk distribution. And now you can configure and reconfigure your new Incredible PBX phones from the convenience of the Incredible PBX GUI.
The lynchpin of Incredible PBX 2020 and beyond is ClearlyIP components which bring management of FreePBX modules and SIP phone integration to a level never before available with any other Asterisk distribution. And now you can configure and reconfigure your new Incredible PBX phones from the convenience of the Incredible PBX GUI.
 VitalPBX is perhaps the fastest-growing PBX offering based upon Asterisk with an installed presence in more than 100 countries worldwide. VitalPBX has generously provided a customized White Label version of Incredible PBX tailored for use with all Incredible PBX and VitalPBX custom applications. Follow this link for a free test drive!
VitalPBX is perhaps the fastest-growing PBX offering based upon Asterisk with an installed presence in more than 100 countries worldwide. VitalPBX has generously provided a customized White Label version of Incredible PBX tailored for use with all Incredible PBX and VitalPBX custom applications. Follow this link for a free test drive!
 Special Thanks to Vitelity. Vitelity is now Voyant Communications and has halted new registrations for the time being. Our special thanks to Vitelity for their unwavering financial support over many years and to the many Nerd Vittles readers who continue to enjoy the benefits of their service offerings. We will keep everyone posted on further developments.
Special Thanks to Vitelity. Vitelity is now Voyant Communications and has halted new registrations for the time being. Our special thanks to Vitelity for their unwavering financial support over many years and to the many Nerd Vittles readers who continue to enjoy the benefits of their service offerings. We will keep everyone posted on further developments.
Some Recent Nerd Vittles Articles of Interest…
Hold On to Your Wallet: Another Huge VoIP Phone Bill May Be Lurking
We interrupt our regularly scheduled content to bring you an urgent security alert. A couple days ago, a FreePBX® user reported unusual call activity. He traced the calls to a System Admin Dashboard module that was linked back to an IP address in the Netherlands. When the problem was reported, the FreePBX Community Manager quite accurately noted that it wasn’t FreePBX code. When a second user reported the exact same exploit, alarm bells apparently went off.
Further digging by the FreePBX Dev Team found that the legacy ARI module (once again) had been compromised, this time with a Remote Code Execution and Privilege Escalation exploit. Previous security vulnerabilities in this module led the PBX in a Flash developers many years ago to abandon the FreePBX security model in favor of Apache security so that we could totally block ARI access unless the user had administrator privileges. We want to stress that this wasn’t the fault of any of the current FreePBX developers. Instead, our move to Apache security was based upon our realization that this old legacy code was difficult to maintain because none of the original developers were still around. To their credit, the FreePBX developers have introduced a new User Control Panel with the strongest recommendation that the older ARI module be abandoned. Unfortunately, it still exists on all but the very latest FreePBX 12 systems including FreePBX 12 systems which were upgraded from a previous release. In addition, FreePBX 12 now provides checksum protection for all registered modules which will go a long way toward eliminating attacks such as this. So what can you do to protect your servers and your wallet today? For openers, upgrade your FreePBX fw_ari module NOW and clean the malicious module off your server:
rm -rf AMPWEBROOT/admin/modules/admindashboard amportal a ma upgrade fw_ari
If you encounter an error that FreePBX cannot connect to the Asterisk Manager, do the following from the Linux CLI:
sed -i 's|localhost|127.0.0.1|' /etc/freepbx.conf amportal restart amportal a r
Protecting Your Server from Remote VoIP Attacks
Let’s approach the long-term solution on several levels starting with vulnerability exposure. If you can access TCP ports 22 (SSH) and 80 (HTTP) and TCP/UDP port 5060 (SIP) of any of your Asterisk® and FreePBX-based servers anonymously from the Internet, you’re either nuts or rich.
We’ve cautioned against this for nearly a decade and yet even some developers still configure Asterisk and FreePBX-based servers with port 80 Internet exposure. Why? We can only assume it’s because it makes their job of accessing and maintaining these systems easy. Don’t do it! There still are numerous ways to gain access to the FreePBX GUI on any server. Here’s our short list…
Safest. Put your server behind a hardware-based firewall with no Internet port exposure. Then use a VPN to access the FreePBX GUI. In a perfect world, you can run a VPN on all of your VoIP phones so that you have end-to-end protection for your server and all of your users.
Safer. If a hardware-based firewall isn’t possible, use the Linux IPtables firewall and lock down all the ports on your server, especially TCP ports 22 and 80 and TCP/UDP port 5060. Then create a WhiteList of IP addresses that need access privileges. It’s worth stressing that Fail2Ban is completely worthless when it comes to security vulnerabilities such as the ARI RCE flaw because the bad guys walk right in without even being challenged for a password.
Safe. If you need remote access from various remote locations and these sites have dynamic IP addresses, then deploy the Port Knocker technology in addition to locking down your server with the IPtables firewall. This lets you gain temporary access to your server without providing a blank check (literally) to everybody on the Internet. There’s a reason it’s called the World Wide Web and not the Good Guys Web!
Worse. Exposing TCP port 5060 and UDP port 5060 to public Internet access is dangerous. Some providers unfortunately still require direct access to 5060 to make VoIP calls with SIP. TIP: Switch to a provider that allows SIP registrations so that you don’t have to expose port 5060 directly to the Internet EVER!
Worser. Pardon our grammar, but exposing TCP port 22 to public Internet access is a bad idea. At the very least, change the SSH port so that typical port scanners don’t discover your open SSH port. SSH has been compromised in the past. It probably will happen again, or it may have already happened and we just don’t (yet) know about it. Fail2Ban helps with SSH attacks, but it’s not infallible particularly when high performance servers are used in the attacks. Fail2Ban has to scan your logs and, before it can do that, it has to have a sufficient time slice to accomplish the scan, something that may never happen with an attack launched from a platform such as Amazon EC2.
Worst. Never expose TCP port 80 to public Internet access. If you do, then you obviously haven’t had the pleasure of trying to maintain a public web server. TIP: Unless you are a web expert or sleep with one, don’t do it EVER! Earlier this week BASH provided a revolving door to your Internet assets using simple web requests. Earlier this year, OpenSSL was compromised. There will be another vulnerability because it’s the easiest attack target. So it’s just a matter of time until your server is compromised unless you deploy an effective firewall that blocks public access to port 80.
Server Design Still Matters
For our own PBX in a Flash and Incredible PBX users, you can sleep well tonight. Today’s vulnerability is mostly academic for you. PBX in a Flash blocks all access to ARI without the maint password. Incredible PBX blocks all access to ARI through its IPtables WhiteList. It’s still a good idea to apply the FreePBX update just to be double-safe. And Incredible PBX users will have the patch applied the next time they log into their server as root. For everyone else using FreePBX, keep reading.
With our Incredible PBX open source project, we provide state-of-the-art security methodology. While it is not infallible, all of the code is freely available for any and all VoIP developers to review, improve, and deploy. We would encourage our fellow VoIP developers to do so. There were reasons in the past for not deploying Apache security. After all, it lacks the flexibility of the FreePBX security model, and Apache also can be compromised. But we can’t think of any reason today for not deploying a hardened, preconfigured IPtables firewall AND a functional WhiteList as an integral component in every VoIP server install. This is especially important for any product deployed with the FreePBX GUI. Our Travelin’ Man 3 WhiteList implementation has been available for more than 2½ years! While there are downsides to any sort of push technology, we also believe the Incredible PBX (opt-in) update service is worth a careful look. It has been a godsend for us. With every new login, the server checks for important updates and processes them unless the administrator chooses not to use the service.
Keep in mind that FreePBX masquerading as the asterisk user has complete read/write privileges to virtually every Asterisk and web asset on your server. Any compromise is extremely dangerous because the asterisk user on these platforms has such expansive privileges. We recently encountered a trojan authorization lurking inside the permissions list of Asterisk’s manager.conf table. The matter is still under investigation so we can’t reveal much more other than to note that the entry was harmless on the few affected Incredible PBX servers because of the hardened IPtables WhiteList which is a key component of every Incredible PBX server. Had this happened on a server with no firewall protection, the intruder would have had complete access to the Asterisk AMI which pretty much gives the intruder a blank check to Asterisk… using your checkbook. The silver lining was the Incredible PBX update utility which provided a quick way to remove the vulnerability.
The FreePBX Dev Team’s efforts to design and deploy a checksum-based system for FreePBX 12 modules is certainly a step in the right direction. We think more safeguards are warranted. We already are exploring new ways to provide alerts when critical Asterisk or FreePBX resources are modified on PBX in a Flash and Incredible PBX servers. Something akin to the Mac’s admin authorization requirement before critical Asterisk or FreePBX changes are made would be ideal, but we have some other ideas as well. Stay tuned!
Originally published: Wednesday, October 1, 2014

Need help with Asterisk? Visit the PBX in a Flash Forum.
Special Thanks to Our Generous Sponsors
FULL DISCLOSURE: ClearlyIP, Skyetel, Vitelity, DigitalOcean, Vultr, VoIP.ms, 3CX, Sangoma, TelecomsXchange and VitalPBX have provided financial support to Nerd Vittles and our open source projects through advertising, referral revenue, and/or merchandise. As an Amazon Associate and Best Buy Affiliate, we also earn from qualifying purchases. We’ve chosen these providers not the other way around. Our decisions are based upon their corporate reputation and the quality of their offerings and pricing. Our recommendations regarding technology are reached without regard to financial compensation except in situations in which comparable products at comparable pricing are available from multiple sources. In this limited case, we support our sponsors because our sponsors support us.
 BOGO Bonaza: Enjoy state-of-the-art VoIP service with a $10 credit and half-price SIP service on up to $500 of Skyetel trunking with free number porting when you fund your Skyetel account. No limits on number of simultaneous calls. Quadruple data center redundancy. $25 monthly minimum spend required. Tutorial and sign up details are here.
BOGO Bonaza: Enjoy state-of-the-art VoIP service with a $10 credit and half-price SIP service on up to $500 of Skyetel trunking with free number porting when you fund your Skyetel account. No limits on number of simultaneous calls. Quadruple data center redundancy. $25 monthly minimum spend required. Tutorial and sign up details are here.
 The lynchpin of Incredible PBX 2020 and beyond is ClearlyIP components which bring management of FreePBX modules and SIP phone integration to a level never before available with any other Asterisk distribution. And now you can configure and reconfigure your new Incredible PBX phones from the convenience of the Incredible PBX GUI.
The lynchpin of Incredible PBX 2020 and beyond is ClearlyIP components which bring management of FreePBX modules and SIP phone integration to a level never before available with any other Asterisk distribution. And now you can configure and reconfigure your new Incredible PBX phones from the convenience of the Incredible PBX GUI.
 VitalPBX is perhaps the fastest-growing PBX offering based upon Asterisk with an installed presence in more than 100 countries worldwide. VitalPBX has generously provided a customized White Label version of Incredible PBX tailored for use with all Incredible PBX and VitalPBX custom applications. Follow this link for a free test drive!
VitalPBX is perhaps the fastest-growing PBX offering based upon Asterisk with an installed presence in more than 100 countries worldwide. VitalPBX has generously provided a customized White Label version of Incredible PBX tailored for use with all Incredible PBX and VitalPBX custom applications. Follow this link for a free test drive!
 Special Thanks to Vitelity. Vitelity is now Voyant Communications and has halted new registrations for the time being. Our special thanks to Vitelity for their unwavering financial support over many years and to the many Nerd Vittles readers who continue to enjoy the benefits of their service offerings. We will keep everyone posted on further developments.
Special Thanks to Vitelity. Vitelity is now Voyant Communications and has halted new registrations for the time being. Our special thanks to Vitelity for their unwavering financial support over many years and to the many Nerd Vittles readers who continue to enjoy the benefits of their service offerings. We will keep everyone posted on further developments.
Some Recent Nerd Vittles Articles of Interest…


 JUST RELEASED: Visit the Incredible PBX Wiki
JUST RELEASED: Visit the Incredible PBX Wiki