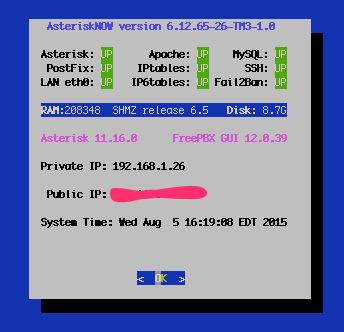
The Ultimate Linux Sandbox in the Cloud for Less Than a $35 Raspberry Pi 2
Every few years we like to drop back and take a fresh look at the best way to get started with Linux. For those coming from the Windows World, it can be a painful process. Learning with a Cloud-based server can be especially dangerous because of the security risks. And then there’s the cost factor. Not everyone has several hundred dollars to buy hardware and, frankly, learning about Linux on a $35 Raspberry Pi can drive most newbies to drink.… Read More ›