Introducing OSS Endpoint Manager for FreePBX 16 & Incredible PBX 2027
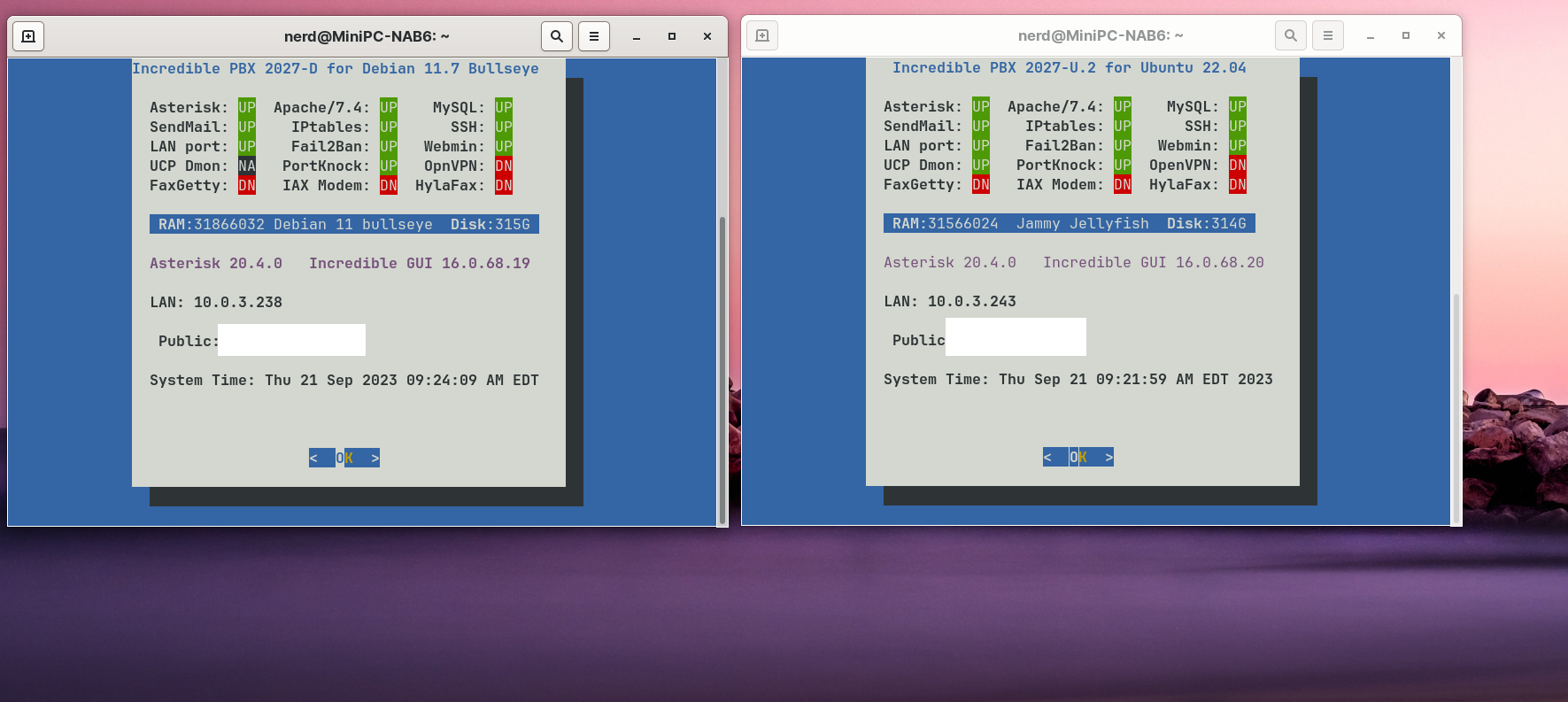
If you’ve been searching for a free, open source provisioning system for your SIP telephones and you’re using Incredible PBX 2027 or other FreePBX® 16 platforms, your prayers have been answered thanks to the hard work of Bill Simon. What this buys you (for free) is a quick way to configure SIP devices from most of the major players shown above including Aastra, AudioCodes, Cisco, Linksys, CloudTC, Digium, Grandstream, Intelbras, Mitel, Norphonic, Patton, Polycom, Snom, Thomson, Unidata, Xorcom, and Yealink.… Read More ›








 JUST RELEASED: Visit the Incredible PBX Wiki
JUST RELEASED: Visit the Incredible PBX Wiki
