
Last week we introduced a new methodology for deploying Incredible PBX® and Asterisk® on the wide open Internet. And this week we’ve put all the pieces together in a One-Minute Installer that will transform any Incredible PBX 13-13.10 server into a public-facing server platform in under a minute. Today you not only get the cupcake, but also some of the sprinkles in the form of tips or scripts to whitelist providers and users, to adjust countries on the blacklists, to add IP addresses to the blacklist, and to update our default VoIP Blacklist which now blocks over 83,000 suspicious IP addresses worldwide. Stay tuned for more.
Is It Safe?
Let’s first cover our deployment strategy so you can decide whether a public facing PBX is the right choice for you or your organization. What we mean by "exposed to the Internet" is that all of your SIP traffic is opened for public access. It doesn’t mean everybody gets free admission, but it does allow everyone to come to the door and at least knock. We still protect web access to your server with a whitelist of IP addresses, and SSH access is hidden behind a port number of your choice to protect you from the script kiddies. Is it as safe as the traditional Incredible PBX platform that is totally hidden from public view by the Travelin’ Man 3 firewall whitelist? Obviously not. But what you gain is what we had with the traditional Ma Bell phone system. Anybody can call you, but it’s up to you to determine whether to answer or block the calls. The major difference is there was a cost of calling random numbers in the old days. With VoIP technology, all of the calls are free so long as the caller has an Internet connection and a SIP client. We believe the platform is relatively safe today, but there is always a chance of SIP flooding or some zero-day vulnerability that could put your server at risk. If you’re not comfortable with that risk, now would be a good time to stop reading. Stick with the traditional Incredible PBX platform and avoid the worries of SIP attacks. The bad guys can’t see your server, and you still can be reached by calls to your PSTN number.
Changing Your Mindset About Security
Deploying a public-facing PBX does require an attitude adjustment. Behind the security of an airtight firewall, passwords for extensions, voicemail, and trunks didn’t much matter because the bad guys couldn’t find you much less get the necessary access to attempt to decipher your passwords. THAT HAS NOW CHANGED! You should immediately create new passwords that are as secure as you would use for your bank account because some folks will be trying to figure them out shortly. And, once they do, if you have VoIP services that allow calls to anywhere, your phone bill can skyrocket in a matter of minutes. You’ve been warned. If you have automatic replenishment of funds with one or more VoIP providers, change that now. And set up low balance notifications instead. Fund your VoIP provider accounts with amounts you can stand to lose in a worst case scenario. Better safe than sorry… and broke!
Choosing FQDNs for Your Server
There’s another important safeguard in today’s implementation, and that’s fully-qualified domain names (FQDNs) for your server. Without knowing your FQDN, nobody will be able to make a SIP connection to your PBX. Guessing your IP address won’t help because we automatically block all of those calls. And, once any caller attempts to connect in that way, they will be blocked from further access for a very long time by the Fail2Ban service. You have the option of using a single FQDN for both incoming calls and for registering SIP phones to your extensions. You also may use two separate FQDNs, one for incoming calls from the public and another for SIP phone registrations. Despite what some pundits would say, security through obscurity matters. Using less obvious FQDNs dramatically reduces the likelihood that your server can be attacked. This is especially important in the case of a SIP registration FQDN. Making this FQDN as obscure as possible protects your server in much the same way that a password would. So give serious consideration to whether your FQDN will be known or guessed by the general public. If so, deploy a second obscure one for registrations.
Deployment Prerequisites
That’s all we’re going to say about security. We’re now going to turn our attention to deployment. Before running the One-Minute Installer, there are some prerequisites. Here’s the short list:
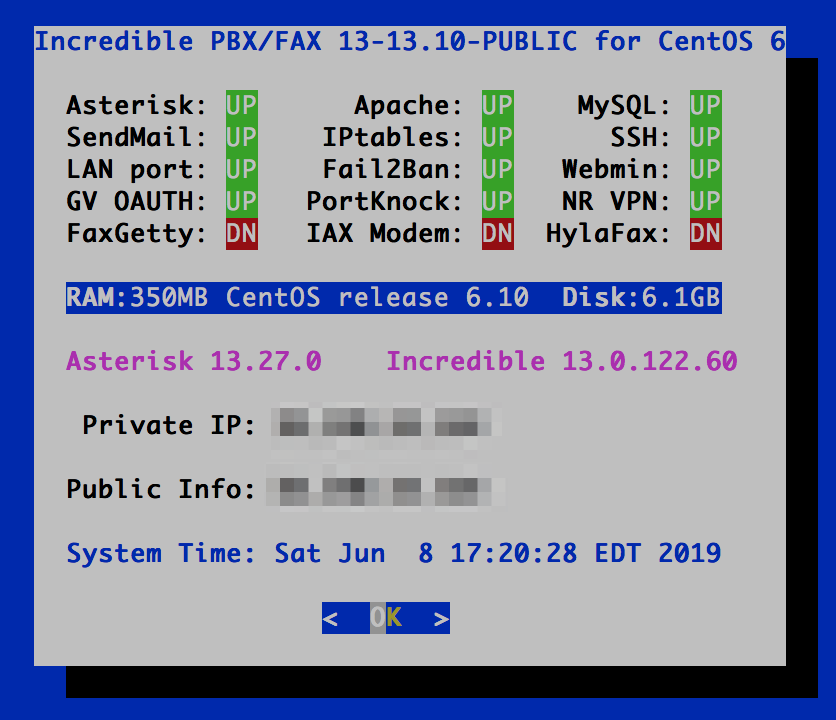
- Functioning Incredible PBX 13-13.10 server with CentOS 6
- KVM (not OpenVZ) Cloud Platform with 1GB+ RAM
- Public, Static IPv4 Address for your server
- One or two FQDNs pointed to your server
- Whole Enchilada installed, if desired
- Incredible Fax installed, if desired (requires reboot)
- Preconfigured extensions & voicemail accounts with SECURE PASSWORDS
We’ve provided the link above to get your Incredible PBX 13-13.10 server up and running. This must be deployed on a Cloud-based KVM platform using CentOS 6 on a KVM (not OpenVZ) platform with a static IP address and a minimum of 1GB of RAM and a 20GB disk. The KVM platform is mandatory because we’ll be using ipset (which won’t work with OpenVZ platforms) to block entire countries as well as to set up our VoIP Blacklist. You’ll need at least one and preferably two FQDNs pointed to the IP address of your PBX. If you plan to use the Incredible PBX apps, then make sure to install the Whole Enchilada and Incredible Fax components before you transform your PBX into a public-facing server. And, as previously mentioned, tighten up ALL of your passwords for SSH and web access as well as for all of your extension secrets and voicemail PINs. It’s also a good idea to create the extensions you plan to make available for incoming calls although these can be added later as well.
UPDATE: CentOS 7 support with Incredible PBX 13-13.10 now has been added.
Choosing a KVM Platform
There are numerous cloud providers that offer a KVM platform. Choosing one that’s a perfect fit depends upon your budget obviously. For rock-solid dependability and little risk of provider implosion, we recommend Digital Ocean, Vultr, and OVH.1 If you’re just experimenting and can recover if your provider happens to suddenly go out of business, then the LowEndBox KVM offerings will save you some money. We don’t recommend CloudAtCost.
Converting to a Public-Facing PBX
Once you’ve completed the steps above and verified that your PBX is functioning reliably, you’re ready to download and run the One-Minute Installer to convert Incredible PBX into a public-facing server.
WARNING: Before you proceed, make certain that you log out any extensions that are registered using the IP address of the PBX as opposed to the FQDN of your server. Otherwise, these extensions may find their IP addresses locked out by Fail2Ban since SIP extension registrations by IP address will be blocked once the conversion to a public server is finished. After the update, if you find extensions that won’t register, the first thing to do is to issue the command: iptables -nL. See if the extension’s IP address is blocked. If it is, change the extension’s SIP registration to point the FQDN of the server as opposed to its IP address. Then you can unblock the IP address with this command using the extension’s actual IP address:
fail2ban-client set asterisk unbanip xxx.xxx.xxx.xxx
Now let’s proceed. Log into your server as root with SSH/Putty and issue these commands:
cd /root wget http://incrediblepbx.com/go-public.tar.gz tar zxvf go-public.tar.gz rm -f go-public.tar.gz ./GO-PUBLIC
Modifying the Blocked Countries List
As part of the install, all of the IP addresses from a number of countries were blocked using ipset in conjunction with the IPtables firewall. You can add or change the countries being blocked by making modifications in two places: (1) /etc/sysconfig/iptables beginning at line #69 and (2) /etc/blockem.sh on line #7. Be advised that every country blocked in IPtables requires a separate DROP line and the same country must also be enumerated on line #7 in /etc/blockem.sh. Otherwise, the IPtables firewall startup will fail when your server is rebooted or when IPtables is restarted. If a country is blocked on line #7 in /etc/blockem.sh but a DROP line is not added to /etc/sysconfig/iptables, then that country’s IP addresses will NOT be blacklisted when IPtables is restarted or your server is rebooted. Simply stated, the countries blocked in IPtables must match the country list in /etc/blockem.sh. For a current list matching countries with their international country code abbreviations, go here.
Blacklist Update Methodology
As configured, the country blacklists are only updated when the /etc/blockem.sh script is run. This occurs whenever you reboot your server or when you manually run the script. The VoIP Blacklist is updated nightly by a cron job which runs the /etc/update-voipbl.sh script.
Adding Extensions to Your SIP WhiteList
For the time being, you can manually adjust the extension listing that controls incoming SIP call access to your PBX. Only extensions included in this list are made available to receive incoming calls using the SIP URI syntax of 701@your.fqdn.com. First, you will need to edit extensions_override_freepbx.conf in /etc/asterisk. Once you’ve saved your changes, reload your dialplan: asterisk -rx "dialplan reload"
Beginning on line 31 of extensions_override_freepbx.conf, you will see a series of lines that actually authorize anonymous SIP connections with your server. There are two numeric entries and also two alpha entries to access the News and Weather apps on your server. Below them are the extensions you whitelisted when you ran the One Minute Installer above. The 13 entry in each line of the dialplan is required for all extensions to be enabled. You can add additional extensions by cloning the syntax of one of the existing entries. Be sure to enter the new extension number in BOTH places on each line that you add. The first entry corresponds to the left side of the SIP URI, e.g. 947@your.FQDN.com. The second entry tells Asterisk the extension to which to send the incoming call. Samples also are provided in the comments for redirecting incoming calls to outbound destinations. See also last week’s article.
exten => 947,13,Dial(local/947@from-internal) exten => 951,13,Dial(local/951@from-internal) exten => news,13,Dial(local/951@from-internal) exten => weather,13,Dial(local/947@from-internal)
Adding IP Addresses to Your IPtables BlackList
You can manually add BlackList entries to your server using ipset; however, keep in mind that these entries will be overwitten when the VoIP Blacklist is updated each night. The recommended procedure is to first add them to ipset using the following command with the actual IP address to be blacklisted: ipset add voipbl xx.xx.xx.xx
Then visit the VoIP BlackList site and add the same IP address in the Blacklist Submission form. Multiple IP addresses can be added by separating every entry with a space.
Adding IP Addresses to Your IPtables WhiteList
You can whitelist additional IP addresses to enable access to your PBX that takes precedence over the blacklists by using the existing add-ip and add-fqdn utilities included in the /root folder. These were both modified to accommodate the public-facing Incredible PBX design.
Last week we got bitten by the age-old problem with BlackLists, namely that the bad guys populate them with IP addresses of places you actually want to go, such as CallCentric and Skyetel. Without a whitelist of safe sites, a blacklist is worse than worthless. So the way this works in Incredible PBX is the whitelist entries are moved to the top of the pecking order so that they take precedence in IPtables processing. The IPtables design works like this. Once a packet qualifies as safe by being accepted, the rest of the IPtables rules are ignored. Enjoy!
Originally published: Monday, June 10, 2019

Need help with Asterisk? Visit the VoIP-info Forum.
Special Thanks to Our Generous Sponsors
FULL DISCLOSURE: ClearlyIP, Skyetel, Vitelity, DigitalOcean, Vultr, VoIP.ms, 3CX, Sangoma, TelecomsXchange and VitalPBX have provided financial support to Nerd Vittles and our open source projects through advertising, referral revenue, and/or merchandise. As an Amazon Associate and Best Buy Affiliate, we also earn from qualifying purchases. We’ve chosen these providers not the other way around. Our decisions are based upon their corporate reputation and the quality of their offerings and pricing. Our recommendations regarding technology are reached without regard to financial compensation except in situations in which comparable products at comparable pricing are available from multiple sources. In this limited case, we support our sponsors because our sponsors support us.
 BOGO Bonaza: Enjoy state-of-the-art VoIP service with a $10 credit and half-price SIP service on up to $500 of Skyetel trunking with free number porting when you fund your Skyetel account. No limits on number of simultaneous calls. Quadruple data center redundancy. $25 monthly minimum spend required. Tutorial and sign up details are here.
BOGO Bonaza: Enjoy state-of-the-art VoIP service with a $10 credit and half-price SIP service on up to $500 of Skyetel trunking with free number porting when you fund your Skyetel account. No limits on number of simultaneous calls. Quadruple data center redundancy. $25 monthly minimum spend required. Tutorial and sign up details are here.
 The lynchpin of Incredible PBX 2020 and beyond is ClearlyIP components which bring management of FreePBX modules and SIP phone integration to a level never before available with any other Asterisk distribution. And now you can configure and reconfigure your new Incredible PBX phones from the convenience of the Incredible PBX GUI.
The lynchpin of Incredible PBX 2020 and beyond is ClearlyIP components which bring management of FreePBX modules and SIP phone integration to a level never before available with any other Asterisk distribution. And now you can configure and reconfigure your new Incredible PBX phones from the convenience of the Incredible PBX GUI.
 VitalPBX is perhaps the fastest-growing PBX offering based upon Asterisk with an installed presence in more than 100 countries worldwide. VitalPBX has generously provided a customized White Label version of Incredible PBX tailored for use with all Incredible PBX and VitalPBX custom applications. Follow this link for a free test drive!
VitalPBX is perhaps the fastest-growing PBX offering based upon Asterisk with an installed presence in more than 100 countries worldwide. VitalPBX has generously provided a customized White Label version of Incredible PBX tailored for use with all Incredible PBX and VitalPBX custom applications. Follow this link for a free test drive!
 Special Thanks to Vitelity. Vitelity is now Voyant Communications and has halted new registrations for the time being. Our special thanks to Vitelity for their unwavering financial support over many years and to the many Nerd Vittles readers who continue to enjoy the benefits of their service offerings. We will keep everyone posted on further developments.
Special Thanks to Vitelity. Vitelity is now Voyant Communications and has halted new registrations for the time being. Our special thanks to Vitelity for their unwavering financial support over many years and to the many Nerd Vittles readers who continue to enjoy the benefits of their service offerings. We will keep everyone posted on further developments.

- Digital Ocean and Vultr provide modest referral credits to Nerd Vittles for those that use our referral code. It in no way colors our recommendations regarding these two providers, both of whom we use extensively. [↩]



Support for CentOS 7 now has been added to the installer.