We’ve previously documented how to change Incredible PBX 2021 and Incredible PBX 2020 into PUBLIC-facing PBXs. What that means is that authorized users could still connect to your PBX regardless of where they may be located without having to worry about whitelisting IP addresses. To suggest that the procedure was convoluted is a bit of an understatement. So today we offer a simplified solution that you can deploy in a couple of minutes. It lacks some of the safeguards of the earlier releases, but it remains secure so long as you don’t employ a readily decipherable FQDN for your PBX. The idea here is to block communications access to your PBX using its public IP address and allow access by those that know the fully-qualified domain name (FQDN) of your PBX. You can also restrict the extensions that are accessible. And SSH access to your PBX will be protected by assigning a random port number or by requiring public key authentication for access.
Prerequisites. To get started, you’ll obviously need a cloud-based Incredible PBX 2020 or 2021 platform running CentOS 7, Debian 10, or Raspbian. Next, you’ll need these items:
- Public IP Address of your server
- FQDN linked to the public IP address
- Random SSH port for SSH access to PBX
- List of secure extensions to enable for SIP URI access
- IP Addresses to WhiteList for Access to the Web GUI
1. Deciphering Public IP Address of Your PBX
After logging into your PBX as root, you can execute pbxstatus to decipher the public IP address of the PBX.
2. Obtaining an FQDN for Your PBX
Security through obscurity provides the critical layer of protection for your server so choose an FQDN carefully. sip.yourname.com provides little protection while f246g.yourname.com pretty much assures that nobody is going to guess your domain name. This is particularly important with SIP registrations because registered extensions on your PBX can obviously make phone calls that cost you money. If you don’t have your own domain, you can always obtain a free hostname from a service such as NoIP.com.
3. Securing SSH Access to Your PBX
Whatever you do, don’t leave SSH access via port 22 exposed on your PBX. In the time it took to create a new PBX on CloudAtCost, there were over 400 attempted logins to the default SSH port of the new server. The simplest (but least secure) method to avoid these script kiddie attacks is to change the port number for SSH access to your server. We suggest using the year you were born as the port number because it’s easy to remember. Edit /etc/ssh/sshd_config and uncomment the Port line replacing 22 with the port number you chose. Then restart SSH: systemctl restart sshd.
The preferable solution to secure SSH is to create and use SSH keys for access and set PasswordAuthentication no in /etc/ssh/sshd_config. Digital Ocean has an excellent tutorial to walk you through the setup process.
4. Choosing Extensions for SIP URI Public Access
With today’s PUBLIC design, exposing an extension for PUBLIC access means anyone in the world that knows the FQDN of your server and the extension number can do two things using any SIP client: (1) they can call you and (2) they can attempt to register to that extension and make calls on your trunks AND your nickel. So only expose extensions for public access if there is a need to connect or call from remote locations. For extensions you decide to expose, make certain that the passwords for these extensions are extremely secure, lengthy, and use numbers with both UPPER and lower case letters. Never use default extension passwords!
5. Whitelisting IP Addresses for Public Web Access
Without enumerating IP addresses for public web access, you won’t be able to connect to the web GUI of your PBX. Down the road, if you wish to add additional IP addresses, you can use /root/add-ip to add them via SSH.
Deploying New PUBLIC Firewall
To get started, log into your server as root and issue the following commands:
cd /tmp wget http://incrediblepbx.com/newpublic.tar.gz tar zxvf newpublic.tar.gz rm -f newpublic.tar.gz
Next, edit /tmp/iptables.base and change the highlighted entries:
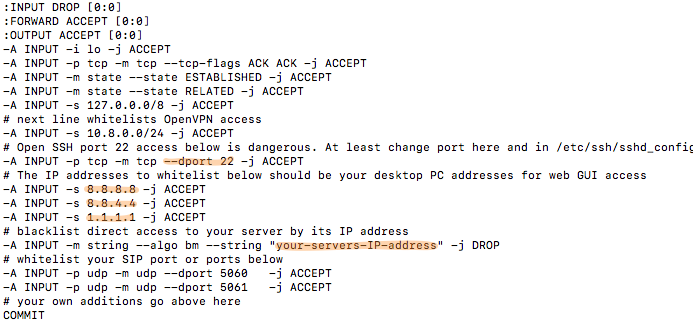
Change port 22 in the dport entry to the SSH port number you chose in Step 3, above.
Change 8.8.8.8, 8.8.4.4., and 1.1.1.1 to actual public IP addresses of desktop machines you wish to use to access the web GUI of your PBX. If you don’t need three entries, comment out the other entries with # at the beginning of each line.
Replace your-servers-IP-address with the actual IP address of your PBX from Step 1, above.
Save the file.
On Debian and Raspbian platforms, issue the following commands:
cd /etc/iptables cp /tmp/iptables.base . mv rules.v4 rules.v4.orig cp iptables.base rules.v4
On CentOS platforms, issue the following commands:
cd /etc/sysconfig cp /tmp/iptables.base . mv iptables iptables.orig cp iptables.base iptables
Using Incredible PBX PUBLIC with Asterisk
The first line of defense with this PUBLIC implementation is your FQDN. Second is the IPtables firewall setup above. And third is the Asterisk® extensions configuration in extensions_override_freepbx.conf. Here’s how to configure it. Edit /tmp/extensions_override_freepbx.base and change the highlighted entries:

If there are phone numbers assigned to your PBX that you want processed according to your Inbound Routing rules, duplicate the first highlighted line above and, for each trunk, replace 8881234567 with your actual DID numbers.
In exten => _.,1 line, replace your-servers-IP-address with the actual IP address of your PBX from Step 1, above.
In exten => _.,10 line, replace your-servers-FQDN with the actual FQDN assigned to your PBX from Step 2, above.
Scroll down in the file to the following section:

Comment out undesired default extensions. Place a semicolon at the beginning of the lines.
For any extensions you wish to add, insert a new line in the following format replacing both 7000 entries with the desired extension number:
exten => 7000,13,Dial(local/7000@from-internal)
Save the file and then execute the following commands to complete the PUBLIC setup:
cd /etc/asterisk cp /tmp/extensions_override_freepbx.base . mv extensions_override_freepbx.conf extensions_override_freepbx.orig cp extensions_override_freepbx.base extensions_override_freepbx.conf fwconsole restart asterisk -rx "dialplan reload" iptables-restart sed -i 's|-A INPUT|-I INPUT|' /root/add-ip sed -i 's|-A INPUT|-I INPUT|' /root/add-fqdn
Calling an Incredible PBX PUBLIC Extension
Any extensions that you have whitelisted in the blue section above can be called from anywhere using any SIP client. Simply enter the SIP URI for the extension in the following format: SIP/extension@your-servers-FQDN
CAUTION: If a caller attempts to call any extension on your PUBLIC server from an extension on another Asterisk server to which the caller is registered, the call will fail if there is a matching extension number on the PUBLIC server and the two servers are not registered to each other. So remember to use unique extension numbers on your PUBLIC server if you expect callers from other Asterisk servers.
Registering Incredible PBX PUBLIC Extension
If you wish to login to a whitelisted extension using a SIP client, enter the extension and password of the extension. For the server address, enter the FQDN of your server. If it’s a PJsip extension, add :5061 to the end of the FQDN.
Switching Back to Incredible PBX Default
Should you change your mind and decide to switch back to the default Incredible PBX setup, it’s simple to do so. Here are the steps.
sed -i 's|Port|#Port|' /etc/ssh/sshd_config cd /etc/asterisk cp -p extensions_override_freepbx.orig extensions_override_freepbx.conf cd /root cd /etc/sysconfig cp -p iptables.orig iptables cd /root cd /etc/iptables cp -p rules.v4.orig rules.v4 asterisk -rx "dialplan reload" iptables-restart systemctl restart sshd
Originally published: Monday, August 16, 2021

Need help with Asterisk? Visit the VoIP-info Forum.
Special Thanks to Our Generous Sponsors
FULL DISCLOSURE: ClearlyIP, Skyetel, Vitelity, DigitalOcean, Vultr, VoIP.ms, 3CX, Sangoma, TelecomsXchange and VitalPBX have provided financial support to Nerd Vittles and our open source projects through advertising, referral revenue, and/or merchandise. As an Amazon Associate and Best Buy Affiliate, we also earn from qualifying purchases. We’ve chosen these providers not the other way around. Our decisions are based upon their corporate reputation and the quality of their offerings and pricing. Our recommendations regarding technology are reached without regard to financial compensation except in situations in which comparable products at comparable pricing are available from multiple sources. In this limited case, we support our sponsors because our sponsors support us.
 BOGO Bonaza: Enjoy state-of-the-art VoIP service with a $10 credit and half-price SIP service on up to $500 of Skyetel trunking with free number porting when you fund your Skyetel account. No limits on number of simultaneous calls. Quadruple data center redundancy. $25 monthly minimum spend required. Tutorial and sign up details are here.
BOGO Bonaza: Enjoy state-of-the-art VoIP service with a $10 credit and half-price SIP service on up to $500 of Skyetel trunking with free number porting when you fund your Skyetel account. No limits on number of simultaneous calls. Quadruple data center redundancy. $25 monthly minimum spend required. Tutorial and sign up details are here.
 The lynchpin of Incredible PBX 2020 and beyond is ClearlyIP components which bring management of FreePBX modules and SIP phone integration to a level never before available with any other Asterisk distribution. And now you can configure and reconfigure your new Incredible PBX phones from the convenience of the Incredible PBX GUI.
The lynchpin of Incredible PBX 2020 and beyond is ClearlyIP components which bring management of FreePBX modules and SIP phone integration to a level never before available with any other Asterisk distribution. And now you can configure and reconfigure your new Incredible PBX phones from the convenience of the Incredible PBX GUI.
 VitalPBX is perhaps the fastest-growing PBX offering based upon Asterisk with an installed presence in more than 100 countries worldwide. VitalPBX has generously provided a customized White Label version of Incredible PBX tailored for use with all Incredible PBX and VitalPBX custom applications. Follow this link for a free test drive!
VitalPBX is perhaps the fastest-growing PBX offering based upon Asterisk with an installed presence in more than 100 countries worldwide. VitalPBX has generously provided a customized White Label version of Incredible PBX tailored for use with all Incredible PBX and VitalPBX custom applications. Follow this link for a free test drive!
 Special Thanks to Vitelity. Vitelity is now Voyant Communications and has halted new registrations for the time being. Our special thanks to Vitelity for their unwavering financial support over many years and to the many Nerd Vittles readers who continue to enjoy the benefits of their service offerings. We will keep everyone posted on further developments.
Special Thanks to Vitelity. Vitelity is now Voyant Communications and has halted new registrations for the time being. Our special thanks to Vitelity for their unwavering financial support over many years and to the many Nerd Vittles readers who continue to enjoy the benefits of their service offerings. We will keep everyone posted on further developments.

